Staking vs yield farming Security
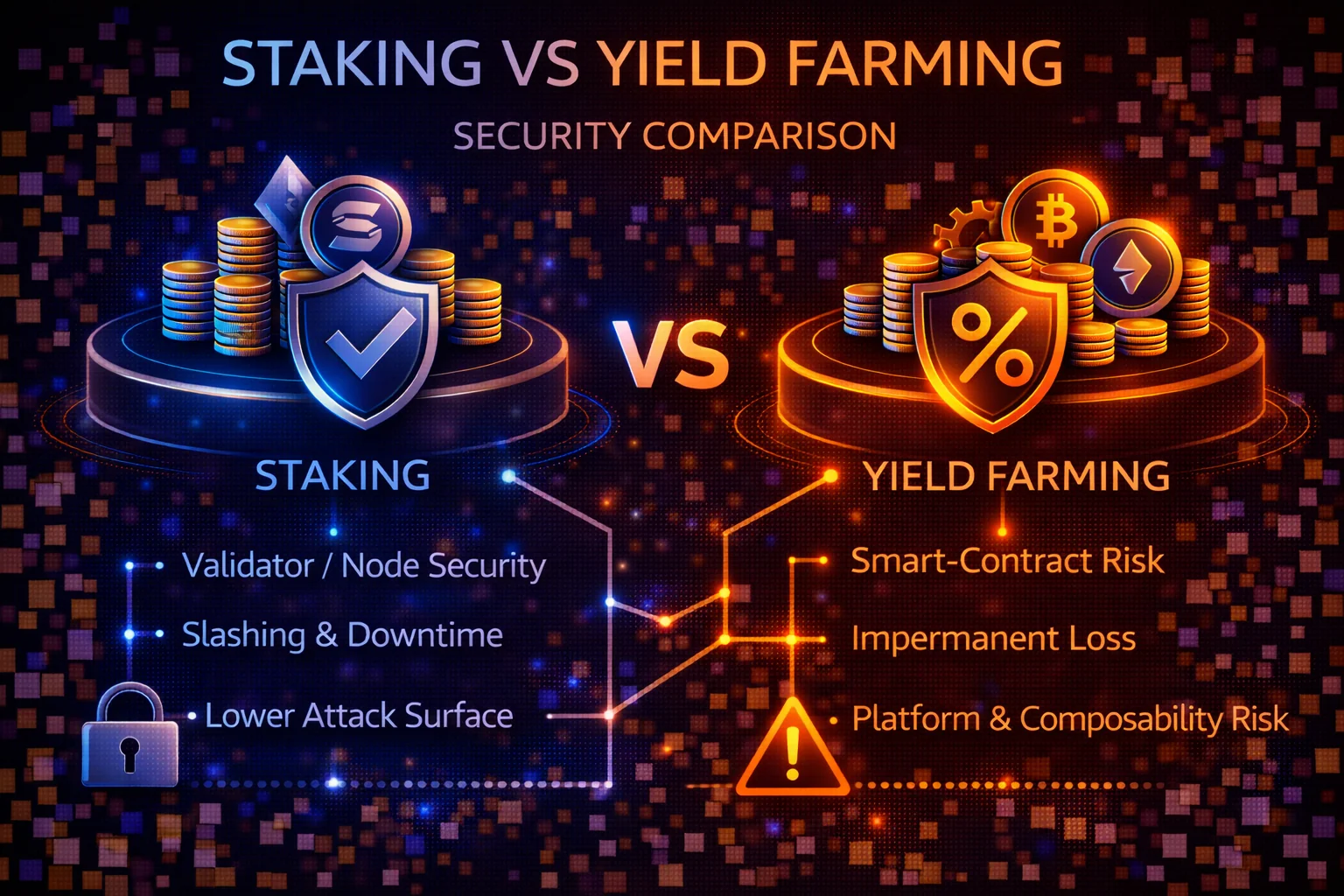
Both staking and liquidity mining can generate earning opportunities, but they expose you to different security risks. This comprehensive guide compares threat models, analyses attack vectors, and provides practical security frameworks to protect your investments.
Introduction
The cryptocurrency landscape has evolved significantly. It now offers sophisticated earning mechanisms beyond simple buy-and-hold strategies. Staking and liquidity mining have emerged as the two primary methods. They generate passive income from digital assets. However, these approaches present fundamentally different security profiles. You need careful analysis and understanding before committing significant capital.
The security considerations extend far beyond simple risk-reward calculations. They encompass technical vulnerabilities and protocol risks. They include smart contract exposures and operational security challenges. These can significantly impact investment outcomes.
Staking represents the more conservative approach from a security perspective. It involves delegation or direct participation in blockchain network validation processes. This earns rewards. This method typically operates within the core protocol layer. It uses established blockchain networks. It benefits from extensive security audits. It uses battle-tested code. It relies on the network's collective security.
The security model relies primarily on the consensus mechanism. It depends on network effects. Risks are generally limited to slashing conditions. They include validator performance and network-level attacks. These would affect the entire blockchain ecosystem.
Major proof-of-stake networks like Ethereum, Cardano, and Solana have undergone years of security testing. They have billions of dollars in value securing their networks. These networks employ sophisticated cryptographic mechanisms. They use economic incentives and distributed validation. This maintains security and prevents attacks.
Liquidity provision introduces multiple layers of additional security complexity. It relies on decentralised finance protocols. It uses smart contracts and liquidity provision mechanisms. This approach requires users to interact with experimental protocols. You deposit funds into smart contracts. These have varying levels of audit coverage. You navigate complex token economies. These can create unexpected risk exposures.
The security model encompasses not only the underlying blockchain security. It also includes smart contract vulnerabilities. It covers protocol governance risks and economic attack vectors. It includes the potential for cascading failures. These occur across interconnected DeFi protocols.
The DeFi ecosystem has experienced numerous security incidents. Over $3 billion was lost to hacks and exploits in 2022 alone. These incidents range from smart contract bugs to flash loan attacks. They include governance token manipulations and bridge exploits. This highlights the additional security layers that farmers must navigate.
Regulatory considerations also play a crucial role in security assessment. Staking generally receives clearer regulatory treatment. DeFi protocols face ongoing scrutiny and potential compliance challenges. This regulatory uncertainty can create additional risks. These include potential protocol shutdowns or access restrictions.
Understanding these security differences is crucial. You need this to make informed decisions about cryptocurrency earning strategies. The potential for loss extends far beyond market volatility. It includes technical failures, protocol exploits, and operational security breaches.
The security landscape continues to evolve rapidly. New attack vectors emerge alongside defensive innovations. Recent developments in cross-chain protocols have added complexity. Liquid staking derivatives introduce new risks. Automated yield optimisation strategies require ongoing security assessment. You need continuous risk management.
Institutional adoption has also influenced security standards. Major financial institutions demand enterprise-grade security measures. They require this before participating in cryptocurrency earning strategies. This institutional involvement has driven improvements. These include custody solutions, insurance coverage, and operational security practices. These improvements span both staking and DeFi protocols.
This comprehensive analysis examines the security frameworks. It covers threat models and risk mitigation strategies for both approaches. It provides practical guidance for protecting investments. You can maximise earning potential in the rapidly evolving cryptocurrency ecosystem of 2025.
Security Overview: The Fundamental Differences
Security in crypto income generation strategies depends on multiple factors: custody models, smart contract complexity, operational requirements, and market dynamics. Understanding these differences is crucial for making informed decisions about risk exposure.
Security Spectrum
The crypto security landscape has evolved significantly, with both staking and yield generation becoming more mature but maintaining distinct risk profiles:
- Staking: Generally simpler with fewer attack vectors, but still subject to validator, slashing, and custody risks
- farming protocols: More complex with multiple smart contract interactions, higher potential returns, but increased attack surface
- Hybrid Approaches: flexible staking and yield optimisation protocols bridge both worlds with combined risk factors
Key Security Principles
- defence in Depth: Multiple security layers to prevent single points of failure
- Risk Proportionality: Security measures should match the value at risk
- Continuous Monitoring: Regular assessment of protocol health and market conditions
- Diversification: Spreading risk across multiple strategies, protocols, and custody models
Comprehensive Threat Models Comparison
Attack Vector Analysis
| Risk Category | Staking Impact | liquidity mining Impact | Likelihood |
|---|---|---|---|
| Smart Contract Exploits | Low (tokenised staking only) | High (multiple contracts) | Medium |
| Custody/Key Compromise | High (if self-custody) | High (if self-custody) | Low |
| Validator Misbehavior | Medium (slashing risk) | N/A | Low |
| IL risk | N/A | High (AMM strategies) | High |
| Protocol Governance Attacks | Low | Medium-High | Low |
| Oracle Manipulation | Low | Medium-High | Medium |
| Bridge Exploits | Low (single chain) | Medium (cross-chain) | Medium |
| Regulatory Action | Medium | Medium | Medium |
Historical Loss Analysis
Major Staking Incidents (2020-2025)
- Ethereum 2.0 Slashing Events: Individual validators lost 1-32 ETH due to double signing or extended downtime
- Lido stETH Depeg (2022): Temporary 5% discount to ETH during market stress
- Terra Luna Collapse (2022): Complete loss for LUNA stakers, highlighting protocol risk
- centralised Exchange Failures: FTX, Celsius affecting staking services
Major DeFi farming Incidents (2020-2025)
- Poly Network Hack (2021): $600 million cross-chain bridge exploit
- Wormhole Bridge Hack (2022): $320 million stolen from Ethereum-Solana bridge
- Euler Finance Hack (2023): $200 million flash loan attack on lending protocol
- Curve Finance Exploit (2023): $70 million lost due to Vyper compiler bug
- Multiple Rug Pulls: Hundreds of smaller protocols with exit scams
Risk Severity Matrix
High Severity (Potential Total Loss):
- Smart contract exploits draining entire protocols
- Private key compromise or custody failures
- Protocol rug pulls or exit scams
- Major validator slashing events
Medium Severity (Partial Loss):
- liquidity risk during market volatility
- Temporary depegs of staking tokens tokens
- Governance attacks changing protocol parameters
- Oracle manipulation affecting prices
Low Severity (Reduced Returns):
- Validator underperformance or small penalties
- Gas cost increases affecting profitability
- Reward token price depreciation
- Temporary protocol downtime
Staking Security Deep Dive
Native Staking Risks
Validator Risks
Slashing Conditions:
- Double Signing: Validator signs conflicting blocks (5-100% penalty)
- Downtime: Extended offline periods (0.01-1% penalty)
- Invalid Attestations: Voting for incorrect chain state
- Correlation Penalties: Higher penalties when many validators fail simultaneously
Mitigation Strategies:
- Choose validators with excellent uptime records (>99.5%)
- Diversify across multiple validators to reduce correlation risk
- Monitor validator performance and switch if needed
- Understand network-specific slashing conditions
Technical Infrastructure Risks
Solo Staking Challenges:
- Hardware Failures: Server downtime leading to penalties
- Network Issues: Internet connectivity problems
- Software Bugs: Client software issues causing slashing
- Key Management: Secure storage of validator keys
Best Practices for Solo Stakers:
- Redundant internet connections and backup power
- Regular software updates and monitoring
- Secure key generation and storage procedures
- Emergency procedures for validator migration
staking derivatives Security
Protocol-Specific Risks
Lido Finance Risk Analysis:
- Smart Contract Risk: Multiple audits but complex codebase
- Validator Set Risk: Curated but centralised validator selection
- Governance Risk: LDO token holders control protocol parameters
- Depeg Risk: stETH may trade below ETH during stress
Rocket Pool Risk Analysis:
- decentralisation Benefits: Permissionless validator onboarding
- Complexity Trade-offs: More complex mechanics increase risk
- Smaller Scale: Less liquidity than Lido but more decentralised
- Insurance Mechanisms: Built-in slashing protection via RPL staking
staking derivatives Token Risks
- Depeg Events: Market stress can cause temporary discounts
- Liquidity Risk: Large redemptions may face delays
- Integration Risk: DeFi protocols may not accept flexible staking tokens
- Regulatory Risk: Potential classification as securities
centralised Staking Services
Exchange Staking Risks
Counterparty Risks:
- Platform Insolvency: Exchange bankruptcy affecting staked funds
- Regulatory Action: Government intervention freezing operations
- Operational Failures: Technical issues or mismanagement
- Withdrawal Restrictions: Limits during market stress
Due Diligence Framework:
- Verify regulatory compliance and licensing
- Check insurance coverage and protection schemes
- Monitor platform financial health and transparency
- Review terms of service and withdrawal policies
- Assess platform security track record
yield generation Security Analysis
Smart Contract Complexity
Multi-Protocol Interactions
farming protocols often involve multiple smart contracts working together, creating compound risk:
- AMM Contracts: Uniswap, Curve, Balancer pool mechanics
- Reward Contracts: Token distribution and vesting logic
- Vault Contracts: Automated strategy execution
- Bridge Contracts: Cross-chain asset transfers
- Oracle Contracts: Price feed dependencies
Common Attack Vectors
Flash Loan Attacks:
- Mechanism: Borrow large amounts, manipulate prices, profit from arbitrage
- Examples: Euler Finance, Cream Finance, Harvest Finance
- Prevention: Time-weighted average prices, flash loan resistant oracles
Governance Attacks:
- Mechanism: Acquire governance tokens, propose malicious changes
- Examples: Beanstalk governance exploit ($182M)
- Prevention: Timelocks, multi-sig requirements, community oversight
Oracle Manipulation:
- Mechanism: Manipulate price feeds to trigger liquidations or arbitrage
- Examples: Various DeFi lending protocol exploits
- Prevention: Multiple oracle sources, circuit breakers, sanity checks
price divergence loss Deep Dive
Mathematical Analysis
Impermanent loss calculation for different price movements:
| Price Change | Impermanent Loss | Break-even Fee Rate |
|---|---|---|
| ±10% | 0.025% | 0.1% annually |
| ±25% | 0.6% | 2.4% annually |
| ±50% | 2.0% | 8% annually |
| ±100% | 5.7% | 23% annually |
| ±200% | 13.4% | 54% annually |
IL Mitigation Strategies
- Correlated Pairs: stETH/ETH, USDC/USDT minimise price divergence
- Concentrated Liquidity: Uniswap V3 ranges for higher fee capture
- Delta-Neutral Strategies: Hedge price exposure with derivatives
- IL Protection: Protocols like Bancor offering IL insurance
Token Economics Risks
Reward Token Sustainability
Unsustainable Tokenomics:
- High Inflation: Excessive token emissions diluting value
- Ponzi Mechanics: New deposits funding old user rewards
- Lack of Utility: Governance tokens without real value accrual
- Vesting Cliffs: Large token unlocks causing price crashes
Sustainable Models:
- Fee Sharing: Tokens backed by real protocol revenue
- Buyback Programs: Protocol profits used to purchase tokens
- Utility Requirements: Tokens needed for protocol functionality
- Deflationary Mechanisms: Token burns reducing supply
Due Diligence Framework
- analyse token distribution and vesting schedules
- Understand revenue sources and sustainability
- Check for real utility beyond governance
- Monitor token unlock events and market impact
- Assess community and developer activity
Custody Models & Risk Analysis
Self-Custody Security
Hardware Wallet Best Practices
Setup and Configuration:
- Purchase Direct: Buy from manufacturer to avoid tampering
- Firmware Verification: Verify authentic firmware signatures
- Secure Generation: Generate seed phrases on device, never digitally
- Multiple Backups: Store seed phrases in multiple secure locations
- Passphrase Protection: Add 25th word for additional security
Operational Security:
- Dedicated Devices: Use separate computers for crypto operations
- Network Isolation: Avoid public WiFi for transactions
- Transaction Verification: Always verify addresses and amounts
- Regular Updates: Keep firmware and software current
Multi-Signature Wallets
Configuration Options:
- 2-of-3: Requires 2 signatures from 3 possible keys
- 3-of-5: Higher security for larger amounts
- Geographic Distribution: Keys stored in different locations
- Role Separation: Different people controlling different keys
Implementation Considerations:
- Choose battle-tested multisig implementations
- Plan for key recovery and succession
- Regular testing of signing procedures
- Documentation of wallet configuration
Custodial Service Evaluation
Institutional Custody Standards
Regulatory Compliance:
- Licensing: Proper financial services licenses
- Insurance: Comprehensive coverage for digital assets
- Audits: Regular SOC 2 Type II audits
- Segregation: Client funds separated from company assets
Technical Security:
- Cold Storage: Majority of funds in offline storage
- Multi-Signature: Distributed key management
- Access Controls: Role-based permissions and monitoring
- Incident Response: Procedures for security breaches
Exchange Custody Risks
Historical Failures:
- Mt. Gox (2014): 850,000 BTC lost to hacking and mismanagement
- FTX (2022): $8 billion user fund shortfall
- Celsius (2022): Bankruptcy freezing user withdrawals
- BlockFi (2022): Insolvency affecting user funds
Risk Mitigation:
- Use only for active trading amounts
- Regular withdrawals to self-custody
- Diversify across multiple exchanges
- Monitor exchange financial health
- Enable all available security features
Smart Contract Risk Assessment
Audit Quality Evaluation
Audit Firm Reputation
Tier 1 Auditors:
- Trail of Bits: Comprehensive security analysis
- ConsenSys Diligence: Ethereum ecosystem specialists
- OpenZeppelin: Security standards and best practices
- Certik: Formal verification and continuous monitoring
Audit Report Analysis:
- Scope Coverage: Percentage of code audited
- Issue Severity: Critical, high, medium, low findings
- Resolution Status: Whether issues were fixed
- Methodology: Manual review vs automated tools
- Timeline: Recent audits vs outdated reports

Bug Bounty Programs
Program Quality Indicators:
- Reward Amounts: Higher bounties attract skilled researchers
- Response Time: Quick acknowledgement and resolution
- Transparency: Public disclosure of resolved issues
- Platform Reputation: Hosted on Immunefi or HackerOne
Smart Contract Verification Standards: Professional security assessment requires comprehensive code review, formal verification methods, and continuous monitoring systems that identify vulnerabilities before exploitation. Advanced protocols implement automated security monitoring, real-time threat detection, and emergency response procedures that protect user funds whilst maintaining operational efficiency and protocol functionality across diverse market conditions and attack scenarios.
- Reward Size: Meaningful payouts ($10k-$1M+)
- Scope Definition: Clear boundaries and rules
- Response Time: Quick acknowledgement and resolution
- Public Disclosure: Transparent reporting of issues
- Continuous Operation: Ongoing vs one-time programs
Code Quality Assessment
Technical Indicators
- Code Complexity: Simpler contracts generally safer
- External Dependencies: Fewer dependencies reduce risk
- Upgrade Mechanisms: Immutable vs upgradeable contracts
- Testing Coverage: Comprehensive test suites
- Documentation Quality: Clear specifications and comments
Governance and Admin Keys
centralisation Risks:
- Admin Keys: Single points of failure or control
- Upgrade Powers: Ability to change contract logic
- Parameter Control: Who can modify critical settings
- Emergency Functions: Pause or shutdown capabilities
decentralisation Indicators:
- Timelocks: Delays before changes take effect
- Multi-Signature: Multiple parties required for changes
- Community Governance: Token holder voting mechanisms
- Immutable Core: Critical functions cannot be changed
Operational Security Best Practices
Transaction Security
Pre-Transaction Checklist
- Address Verification: Double-check recipient addresses
- Amount Confirmation: Verify transaction amounts and decimals
- Gas Price optimisation: Avoid overpaying for transactions
- Slippage Settings: Appropriate slippage for market conditions
- Contract Interaction: Verify you're interacting with correct contracts
Phishing Protection
Common Attack Vectors:
- Fake Websites: Lookalike domains stealing credentials
- Social Media Scams: Fake support accounts and giveaways
- Email Phishing: Fake notifications and urgent actions
- Discord/Telegram: Impersonation and fake announcements
Protection Strategies:
- Bookmark legitimate websites and use only those
- Verify URLs carefully before connecting wallets
- Never share seed phrases or private keys
- Be sceptical of unsolicited contact
- Use official communication channels only
Monitoring and Alerting
Portfolio Tracking Tools
- DeBank: Comprehensive DeFi portfolio tracking
- Zapper: Position management and analytics
- Zerion: Mobile-friendly portfolio dashboard
- APY.vision: Impermanent loss and yield tracking
Alert Configuration
- Price Alerts: Significant asset price movements
- Yield Changes: APY drops below thresholds
- Protocol News: Security incidents or updates
- Transaction Monitoring: Unusual wallet activity
- Liquidation Warnings: Approaching liquidation levels
Incident Response Planning
Emergency Procedures
Protocol Exploit Response:
- Immediate Assessment: Determine if your funds are affected
- Quick Exit: Withdraw funds if protocol is still functional
- Communication: Monitor official channels for updates
- Documentation: Record all transactions for potential claims
- Legal Consultation: Consider options for fund recovery
Wallet Compromise Response:
- Immediate Isolation: Disconnect compromised devices
- Fund Transfer: Move remaining funds to secure wallet
- Revoke Approvals: Cancel all smart contract permissions
- Forensic Analysis: Determine how compromise occurred
- Security Rebuild: Create new wallet with fresh seed phrase
Risk Mitigation Strategies
Diversification Framework
Protocol Diversification
- Maximum Allocation: No more than 25% in any single protocol
- Risk Tiers: Mix of established and newer protocols
- Chain Distribution: Spread across multiple blockchains
- Strategy Types: Combine staking, lending, and liquidity mining
Temporal Diversification
- Gradual Entry: Dollar-cost average into positions
- Staggered Exits: Take profits at different intervals
- Rebalancing Schedule: Regular portfolio adjustments
- Seasonal Considerations: Market cycles and tax implications
Position Sizing Guidelines
Risk-Based Allocation
| Risk Level | Max Allocation | Examples |
|---|---|---|
| Very Low | 50% | Major exchange staking, government bonds |
| Low | 30% | Established tokenised staking (Lido, Rocket Pool) |
| Medium | 15% | Blue-chip DeFi protocols (Aave, Curve) |
| High | 5% | Newer protocols, experimental strategies |
| Very High | 1% | Unaudited protocols, high-risk farms |
Dynamic Adjustment Rules
- Performance-Based: Increase allocation to outperforming strategies
- Risk-Adjusted: Reduce exposure when risk indicators increase
- Market Conditions: Adjust based on overall market volatility
- Personal Circumstances: Modify based on financial situation changes
Insurance and Protection
DeFi Insurance Options
- Nexus Mutual: decentralised insurance for smart contract risks
- InsurAce: Multi-chain coverage for various DeFi risks
- Unslashed Finance: Insurance for staking and DeFi activities
- Bridge Mutual: Coverage for cross-chain bridge risks
Cost-Benefit Analysis
- Premium Costs: Typically 2-10% annually of covered amount
- Coverage Scope: What risks are and aren't covered
- Claim Process: How to file and likelihood of payout
- Break-Even Point: When insurance makes financial sense
Comprehensive Security Checklist
Pre-Investment Security Setup
Wallet and Key Management
- Hardware wallet purchased directly from manufacturer
- Seed phrase generated offline and stored securely
- Multiple backup copies in different locations
- Passphrase protection enabled (25th word)
- Test recovery process with small amounts
- Dedicated computer/browser for crypto operations
- VPN and antivirus software installed and updated
Account Security
- Unique, strong passwords for all accounts
- Two-factor authentication enabled everywhere
- Email security hardened (2FA, recovery options)
- Phone number security (SIM swap protection)
- Social media accounts secured or deactivated
Protocol Due Diligence
Technical Assessment
- Multiple security audits by reputable firms
- Active bug bounty program with meaningful rewards
- Open source code available for review
- Governance structure and admin key analysis
- Time locks and upgrade mechanisms reviewed
- Oracle dependencies and manipulation resistance
Economic Assessment
- Sustainable tokenomics and revenue model
- Reasonable yield expectations (not too good to be true)
- Sufficient liquidity for entry and exit
- Historical performance and volatility analysis
- Team background and track record verified
Operational Security
Transaction Security
- Always verify contract addresses before interacting
- Use official links from bookmarks or verified sources
- Double-check transaction details before signing
- Test with small amounts before large transactions
- Monitor gas prices and avoid overpaying
- Set appropriate slippage tolerances
Ongoing Monitoring
- Regular portfolio tracking and performance review
- Price and yield alerts configured
- Protocol news and security updates monitored
- Wallet activity monitoring for unauthorised transactions
- Regular backup verification and security updates
Risk Management
Position Management
- Position sizes appropriate for risk level
- Diversification across protocols and strategies
- Stop-loss or exit criteria defined
- Regular rebalancing schedule established
- Emergency exit procedures documented
Documentation and Compliance
- All transactions recorded for tax purposes
- Wallet addresses and seed phrases documented securely
- Emergency contact procedures established
- Legal and tax implications understood
- Insurance coverage evaluated and obtained if needed
Professional Implementation Strategies and Best Practices
Strategic Planning and Risk Assessment
Security-focused investors employ risk diversification strategies. They use multiple security models and audit standards. They work across different protocol types. This minimises smart contract risks. It maintains earning potential. Regular security assessment is essential. You need an audit review and risk evaluation. These ensure optimal protection in DeFi environments.
Advanced Security and Operational Excellence
Yield security comparison protocols include comprehensive risk assessment frameworks. They evaluate security audits and operational transparency. This helps investors understand the differences between the securities. You compare staking and yield farming approaches. Professional security analysis includes smart contract auditing. It covers validator reputation assessment. It evaluates platform insurance coverage.
Market Intelligence and Competitive Analysis
Security comparison between staking and yield farming involves assessing smart contract risks. You evaluate validator reliability. You check protocol governance mechanisms. These affect capital safety. Professional investors utilise security audit reports. They use risk assessment frameworks and diversification strategies. This minimises exposure.
Staking typically presents lower security risks. It uses direct blockchain participation. Yield farming involves additional smart contract complexity. It has potential impermanent loss exposure.
Quantitative Security Assessment and Professional Protection Strategies
Advanced Security Metrics and Risk Quantification
Professional security assessment requires sophisticated quantitative frameworks. These measure risk exposure across different cryptocurrency earning strategies. They use comprehensive data analysis, statistical modelling, and predictive risk assessment methodologies. Advanced practitioners utilise Value-at-Risk calculations. They use Monte Carlo simulations and stress testing scenarios. These quantify potential losses under various market conditions. They assess security breach scenarios.
Quantitative security metrics include protocol vulnerability scores. These are based on audit findings. They include smart contract complexity indices and historical exploit frequency analysis. This enables data-driven security decisions. Professional risk assessment incorporates correlation analysis between different protocols. It includes concentration risk calculations and liquidity risk modelling. This provides a comprehensive understanding of portfolio-level security exposure. It covers both staking and yield farming positions.
Statistical Risk Modelling and Predictive Analytics
Advanced statistical models incorporate historical exploit data. They use protocol-complexity metrics and market-volatility patterns. These generate predictive risk scores for different cryptocurrency earning strategies. These models utilise machine learning algorithms. They analyse thousands of data points. These include smart contract audit results, developer activity metrics, and trends in total value locked. They assess governance token distribution patterns. This evaluates protocol security and sustainability.
Predictive analytics frameworks enable early identification of potential security risks. They use pattern recognition algorithms. These detect anomalous behaviour in protocol metrics. They identify unusual transaction patterns and governance proposal activities. Professional risk managers implement these systems. They provide early warning indicators. These enable proactive position adjustments. This happens before security incidents materialise into actual losses.
Bayesian risk models incorporate prior knowledge about protocol types. They consider development teams and audit histories. They continuously update risk assessments as new information becomes available. These dynamic models enable sophisticated risk management. They adapt to changing conditions. They maintain quantitative rigour in security assessment and decision-making processes.
Correlation analysis reveals hidden dependencies between different protocols and strategies. These can create systemic risks during periods of market stress. Advanced practitioners utilise copula models and extreme value theory. They understand tail dependencies and concentration risks. Traditional correlation measures might miss these. This enables more robust diversification strategies.
Institutional Security Frameworks and Enterprise Protection
Enterprise-grade cryptocurrency security frameworks implement multi-layered protection strategies. These combine technical security measures with operational procedures. They include governance controls and comprehensive monitoring systems. These are designed for institutional-scale digital asset management. Professional implementations include segregated custody architectures. They use role-based access controls and comprehensive audit trails. These meet regulatory requirements. They enable sophisticated yield generation strategies.
Institutional security protocols encompass hardware security module integration. They use multi-signature wallet configurations with geographic distribution. They include comprehensive backup procedures. These protect against both technical failures and operational risks. Advanced frameworks include automated threat detection systems. They provide real-time security monitoring and incident response procedures. These minimise potential losses. They maintain operational continuity under various threat scenarios.
Advanced Threat Intelligence and Security Operations
Professional threat intelligence systems aggregate security data from multiple sources. These include blockchain analytics platforms and security research organisations. They provide comprehensive situational awareness for cryptocurrency security management. Security operations centres provide 24/7 monitoring capabilities. They have expertise in blockchain technology and smart contract analysis.
Professional Risk Management
Professional risk management requires systematic approaches. You need position sizing and diversification strategies. You must implement dynamic risk adjustment. This responds to changing market conditions. Advanced practitioners use portfolio optimisation algorithms. These balance yield generation with security considerations.
Automated Security Monitoring
Automated security monitoring systems use artificial intelligence. They analyse blockchain transactions continuously. They identify potential security threats in real-time. These systems detect anomalous activities. They spot unusual transaction volumes and unexpected smart contract calls.
Professional Security Architecture
Professional security architecture requires a comprehensive infrastructure design. It incorporates defence-in-depth principles. It uses zero-trust security models. These are specifically adapted for cryptocurrency operations. Professional implementations include geographically distributed infrastructure. They have redundant systems and failover capabilities.
Regulatory Compliance
Professional cryptocurrency security must address evolving regulatory requirements. Compliance frameworks include comprehensive documentation procedures. They maintain audit trails and regulatory reporting capabilities. These meet institutional standards for digital asset management.
Incident Response and Recovery
Professional incident response procedures include comprehensive playbooks. These cover different types of security incidents. They include automated response systems. Recovery procedures minimise operational disruption. They ensure complete security restoration.
Conclusion
The security comparison between staking and yield farming reveals fundamental differences in risk profiles. These should guide investment decisions. Consider your individual risk tolerance, technical expertise, and investment objectives. Staking emerges as the more secure option for most investors. It offers predictable returns through battle-tested protocols. It has lower technical complexity. It has reduced exposure to smart contract vulnerabilities.
The security model relies primarily on network consensus mechanisms. It depends on the validator's performance. This creates a more straightforward risk assessment framework.
Yield farming offers potentially higher returns. However, it introduces multiple layers of security complexity. These require active management and deep technical understanding. You need this to navigate safely. The interconnected nature of DeFi protocols creates systemic risks. These can result in cascading failures. The experimental nature of many yield farming opportunities exposes investors to risks. These include unaudited smart contracts and novel economic attack vectors.
However, for sophisticated investors willing to accept higher risks, yield farming can provide superior returns. This works when approached with appropriate security measures. You need risk management strategies.
The cryptocurrency security landscape continues to evolve rapidly. New threats emerge alongside technological advances. Staking protocols are implementing additional security features. These include slashing insurance and validator reputation systems. DeFi protocols are adopting formal verification methods. They use bug bounty programs to improve security.
Regulatory developments also play a crucial role in security considerations. There are clearer guidelines for staking activities. DeFi protocols face ongoing scrutiny. This regulatory clarity provides additional security assurance for staking participants. It creates uncertainty for yield farming strategies.
The optimal approach for most cryptocurrency investors involves starting with secure staking strategies. This builds experience and understanding. Then, gradually explore yield farming opportunities with small allocations. This progressive approach allows investors to develop technical skills. They gain risk assessment capabilities necessary for more complex DeFi strategies. They maintain the majority of their holdings in lower-risk staking positions.
Regardless of the chosen strategy, implementing robust security practices remains essential. Use hardware wallets. Implement multi-signature setups. Conduct regular security audits. These protect cryptocurrency investments in the evolving digital asset landscape.
The integration of artificial intelligence and machine learning in security monitoring systems is enhancing threat detection capabilities. Institutional-grade custody solutions are becoming more accessible to retail investors. As the cryptocurrency ecosystem matures, the distinction between staking and yield farming security profiles may blur. Hybrid protocols may offer the predictability of staking combined with the flexibility of yield farming. This creates new opportunities for risk-adjusted returns in the decentralised finance space.
These developments are making sophisticated investment strategies more accessible. They maintain the security standards necessary for long-term wealth preservation. They enable sustainable long-term portfolio growth. Advanced security frameworks now incorporate real-time monitoring, automated risk assessment, and proactive threat mitigation strategies that significantly enhance investor protection across both staking and yield farming activities.
The evolution of decentralised insurance protocols provides additional security layers for both staking and yield farming participants. Coverage options now extend beyond smart contract exploits to include validator slashing events, protocol insolvency, and oracle manipulation attacks. These insurance mechanisms create more robust risk management frameworks that enable investors to pursue higher-yield opportunities whilst maintaining acceptable risk parameters through comprehensive protection strategies.
Important cross-chain security considerations have become increasingly important as multi-chain staking and yield farming strategies gain popularity. Bridge security, cross-chain communication protocols, and interoperability standards require careful evaluation when deploying assets across multiple blockchain networks. Understanding these additional security dimensions is essential for investors seeking to maximise returns through diversified cross-chain strategies whilst maintaining appropriate comprehensive security standards.
Sources & References
- Ethereum Foundation. (2025). Ethereum Staking Guide. Official staking documentation and security best practices.
- Lido. (2025). Lido Documentation. Liquid staking protocol security and architecture.
- Aave. (2025). Aave Security Documentation. DeFi protocol security architecture and audits.
Frequently Asked Questions
- Is staking or yield generation safer?
- Staking is generally safer than farming protocols. Simple staking on established networks like Ethereum has minimal smart contract risk and is backed by network security. liquidity mining involves multiple smart contracts, liquidity pools, and complex interactions that increase vulnerability to exploits and hacks.
- Can I get insurance for staking or DeFi farming?
- Yes, several protocols offer DeFi insurance coverage. Nexus Mutual and InsurAce provide witty contract coverage for major protocols. However, insurance typically covers only smart contract exploits, not market risks, impermanent loss, or protocol insolvency. Always read policy terms carefully.
- How often should I monitor my positions?
- Monitoring frequency depends on strategy complexity. Simple staking requires weekly checks, liquid staking needs weekly monitoring for depeg risk, yield generation demands daily attention, and high-risk strategies require multiple daily checks. During protocol issues or market volatility, increase monitoring frequency significantly.
- What should I do if a protocol gets exploited?
- Act immediately: assess whether your funds are affected, withdraw if the protocol is still functioning, monitor official communications for updates, document all transactions and communications, and consider legal options for significant losses. Speed is critical - exploits can drain funds within minutes.
- Which is better for beginners - staking or farming protocols?
- Staking is significantly better for beginners. It's simpler to understand, has lower technical complexity, requires less active management, and carries substantially lower risk. Start with simple staking on major networks or through regulated exchanges before considering DeFi earning strategies.
← Back to Crypto Investing Blog Index
Financial Disclaimer
This content is not financial advice. All information provided is for educational purposes only. Cryptocurrency investments carry significant investment risk, and past performance does not guarantee future results. Always do your own research and consult a qualified financial advisor before making investment decisions.