How Secure Is Digital Asset Lending?
Cryptocurrency lending has become a cornerstone of the digital asset ecosystem. Offering attractive yields that often exceed traditional financial products by significant margins. However, the security landscape of crypto lending is complex and multifaceted. Encompassing risks from platform failures. Smart contract vulnerabilities to regulatory uncertainty. Market volatility that can impact both lenders and borrowers.
The crypto lending industry has experienced both tremendous growth and significant challenges, with high-profile platform failures like Celsius, Voyager, and FTX highlighting the importance of understanding security risks before committing funds. These events have fundamentally changed how investors approach crypto lending. Emphasising the need for thorough due diligence and risk assessment frameworks.
This comprehensive security analysis examines every aspect of crypto lending safety in 2025. From Centralised platform risks and DeFi smart contract vulnerabilities to custody solutions and regulatory protections. We'll explore real-world security incidents, analyse current best practices,. Provide actionable strategies for minimising risks while participating in crypto lending opportunities.
Introduction
Between 2022 and 2023, crypto lending platforms lost over $20 billion in user funds. Celsius froze $4.7 billion in customer deposits before declaring bankruptcy. BlockFi collapsed owing $10 billion to creditors. Voyager Digital lost $5 billion. FTX misappropriated $8 billion in customer funds. These were not obscure protocols -- they were heavily marketed, well-funded platforms that millions of people trusted with their savings. Understanding why they failed is essential before you deposit a single pound into any lending platform.
The core security question in crypto lending is: who controls your funds, and what can they do with them? CeFi platforms (Nexo, Crypto.com, YouHodler) take custody of your crypto and lend it out to generate yield. You earn interest, but you bear full counterparty risk -- if the platform lends recklessly, invests in risky assets, or commits fraud, your funds can disappear. Celsius was paying 18% APY on stablecoins whilst lending to undercollateralised borrowers and investing in illiquid DeFi positions. When the market crashed, they could not honour withdrawals.
DeFi protocols (Aave, Compound, MakerDAO) eliminate custody risk by locking funds in audited smart contracts that execute automatically. You keep your private keys, and the protocol's code determines who can access funds. However, DeFi introduces code risk: smart contract exploits have drained over $3 billion from DeFi protocols since 2020. The Euler Finance hack in March 2023 alone cost $197 million. Oracle manipulation attacks, governance exploits, and flash loan attacks add further risk layers that CeFi users never face.
Here is a practical security checklist for evaluating any lending platform: (1) Does it publish regular proof-of-reserves audits from a reputable firm? Nexo uses Armanino for real-time attestations. (2) What insurance exists? Nexo carries $775M through Lloyd's of London; Aave has a Safety Module with $400M+ in staked AAVE tokens. (3) How long has it operated without a major incident? Aave: 5+ years, Compound: 6+ years, Nexo: 6+ years. (4) Is the code audited? Aave has been audited by Trail of Bits, OpenZeppelin, and Consensys Diligence. (5) What is the TVL trend? Declining TVL can signal users leaving ahead of problems. Check DefiLlama for real-time data. No platform passes every test perfectly, which is why you should diversify across at least two platforms and never deposit more than you can afford to lose entirely.
This guide examines each risk category in detail with platform-specific data and practical mitigation strategies for each one.
Security Overview
The crypto lending security landscape has improved markedly since the 2022 collapses. The EU's MiCA regulation now requires crypto lending platforms to segregate client funds, maintain capital reserves, and publish regular financial disclosures. In the US, the SEC has brought enforcement actions against platforms offering unregistered securities through lending products. These regulatory developments have forced surviving platforms to raise their standards -- but regulation alone does not eliminate risk. MiCA-compliant platforms can still fail if their lending books turn sour.
Surviving CeFi platforms have adopted stronger transparency measures. Nexo publishes real-time asset attestations through Armanino, showing that customer deposits are fully backed. Crypto.com completed a proof-of-reserves audit with Mazars. On the DeFi side, Aave's Safety Module contains over $400 million in staked AAVE tokens that act as a backstop if the protocol suffers bad debt. Compound has operated for six years with no major exploit. MakerDAO weathered the March 2020 "Black Thursday" crash (where ETH dropped 50% in 24 hours) with only $5.67 million in bad debt -- a stress test that proved its liquidation system works under extreme conditions.
DeFi insurance has matured but remains expensive. Nexus Mutual, InsurAce, and Unslashed Finance offer smart contract cover costing 3-8% of the covered amount annually. A $50,000 Aave position insured for one year costs roughly $1,500-4,000, eating significantly into your yield. The coverage typically pays out only for specific events (smart contract exploits, oracle failures) and excludes governance attacks or economic exploits. For positions under $10,000 on well-audited protocols, self-insurance (simply accepting the risk) is often more cost-effective.

The Cryptocurrency Lending Security Landscape
How Security Has Evolved Since 2022
The digital asset lending sector has undergone significant changes following major platform failures:
- Regulatory Clarity: EU MiCA regulation and clearer US guidelines have improved platform standards
- Insurance Adoption: More platforms offer third-party insurance coverage
- Transparency Requirements: Proof-of-reserves. Regular audits are becoming standard
- Risk Management: Platforms implement better risk controls and diversification
- User Education: Better understanding of risks amongst crypto lenders
Current Threat Landscape
Platform-Level Threats
- Insolvency due to poor risk management
- Regulatory enforcement actions
- Management fraud or misappropriation
- Liquidity crises during market stress
- Cybersecurity breaches and hacks
Protocol-Level Threats
- Smart contract bugs and exploits [1]
- Oracle manipulation attacks
- Governance attacks and hostile takeovers
- Flash loan and MEV attacks
- Cross-chain bridge vulnerabilities
Market-Level Threats
- Extreme volatility affecting collateral
- Liquidity shortages during crises
- Contagion effects from platform failures
- Regulatory changes affecting operations
- Macroeconomic factors impacting yields
CeFi vs DeFi Security: Comprehensive Comparison
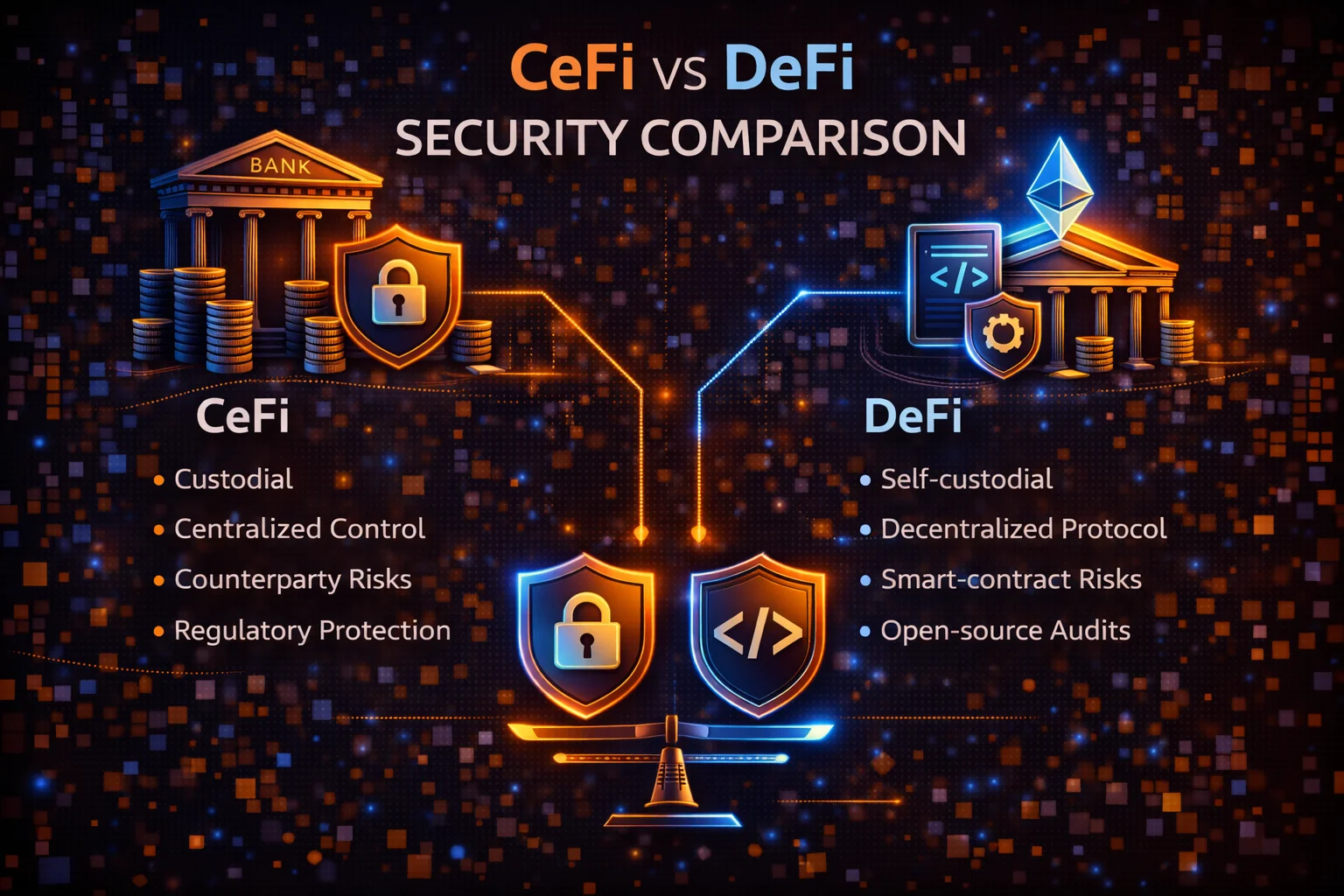
Centralised Finance (CeFi) Security Profile
CeFi Security Advantages
- Regulatory Oversight: Licensed platforms must meet compliance standards
- Insurance Coverage: Many offer FDIC-style or third-party insurance
- Professional Management: Experienced teams managing risk and operations
- Customer Support: Direct support for issues and disputes
- Simplified UX: Reduced user error risk through guided interfaces
- Institutional Backing: Some platforms backed by major financial institutions
CeFi Security Risks
- Custody Risk: Platform controls your private keys and funds
- Counterparty Risk: Platform solvency affects your fund safety
- Rehypothecation: Your funds may be lent to risky borrowers
- Regulatory Risk: Government actions can freeze operations
- Management Risk: Poor decisions or fraud by leadership
- Operational Risk: Internal systems failures or breaches
Decentralised Finance (DeFi) Security Profile
DeFi Security Advantages
- Self-Custody: You maintain control of your private keys
- Transparency: All transactions. Code are publicly auditable
- Permissionless: No KYC requirements or geographic restrictions
- Composability: Can combine multiple protocols for diversification
- Immutability: Smart contracts can't be arbitrarily changed
- Global Access: 24/7 availability without platform restrictions
DeFi Security Risks
- Smart Contract Risk: Code bugs can lead to fund loss
- Oracle Risk: Price feed manipulation can cause liquidations
- Governance Risk: Token holders can make harmful changes
- Complexity Risk: User errors in complex interactions
- Liquidity Risk: Insufficient liquidity for large withdrawals
- Composability Risk: Failures can cascade across protocols
Security Factor Comparison
| Security Factor | CeFi | DeFi | Winner |
|---|---|---|---|
| Custody Control | Platform controlled | User controlled | DeFi |
| Code Transparency | Proprietary/closed | Open source | DeFi |
| Regulatory Protection | Licensed oversight | Minimal regulation | CeFi |
| Insurance Availability | Often available | Limited options | CeFi |
| User Experience | Simple and guided | Complex, error-prone | CeFi |
| Counterparty Risk | High (platform failure) | Low (code-based) | DeFi |
| Technical Risk | Low (managed systems) | High (smart contracts) | CeFi |
| Censorship Resistance | Low (can be shut down) | High (decentralised) | DeFi |
How to Evaluate Platform Security

CeFi Platform Security Checklist
Regulatory and Legal
- ✓ Licensed in major jurisdictions (US, EU, UK)
- ✓ Compliant with local regulations (MiCA, SEC guidelines)
- ✓ Regular regulatory reporting and audits
- ✓ Clear legal structure and jurisdiction
- ✓ Segregated customer funds
Financial Transparency
- ✓ Regular proof-of-reserves reports
- ✓ Third-party financial audits
- ✓ Clear explanation of yield sources
- ✓ Published risk management policies
- ✓ Adequate capitalization and reserves
Security Infrastructure
- ✓ Multi-signature cold storage
- ✓ Regular security audits and penetration testing
- ✓ Bug bounty programs
- ✓ SOC 2 Type II compliance
- ✓ Incident response procedures
Insurance and Protection
- ✓ Third-party insurance coverage
- ✓ Clear coverage terms and limits
- ✓ Excess reserves for customer protection
- ✓ Deposit guarantees or protection schemes
- ✓ Claims process transparency
DeFi Protocol Security Assessment
Smart Contract Security
- ✓ Multiple independent security audits
- ✓ Formal verification of critical functions
- ✓ Active bug bounty programs
- ✓ Time-locked upgrades and governance
- ✓ Battle-tested code (6+ months in production)
Protocol Maturity
- ✓ Significant Total Value Locked (TVL)
- ✓ Long operational history without major exploits
- ✓ Active development and maintenance
- ✓ Strong community and governance participation
- ✓ Integration with other established protocols
Risk Management
- ✓ Conservative collateralization ratios
- ✓ Diversified oracle sources
- ✓ Circuit breakers and emergency procedures
- ✓ Gradual parameter changes through governance
- ✓ Insurance protocol integration options
Learning from Real Security Incidents
Major CeFi Platform Failures
Celsius Network Collapse (2022)
What Happened: Celsius filed for bankruptcy after risky lending practices and liquidity issues. Freezing $4.7 billion in user funds.
Root Causes:
- Excessive risk-taking with customer deposits
- Lack of proper risk management and diversification
- Misleading marketing about fund safety
- Inadequate reserves for customer withdrawals
Lessons learnt:
- High yields often indicate high risk
- Platform marketing doesn't guarantee safety
- Diversification across platforms is essential
- Regulatory oversight provides important protections
FTX Exchange Collapse (2022)
What Happened: FTX filed for bankruptcy amid allegations of misusing customer funds. Affecting lending products and user deposits.
Root Causes:
- Alleged misappropriation of customer funds
- Lack of proper fund segregation
- Poor corporate governance and oversight
- Excessive risk-taking by management
Lessons learnt:
- Even large, reputable platforms can fail
- Fund segregation is crucial for customer protection
- Management integrity is a critical risk factor
- Regular proof-of-reserves is essential
Notable DeFi Security Exploits
Compound Fork Exploit (2024)
What Happened: A flash loan attack exploited a vulnerability in a Compound fork's reward calculation. Draining $15 million.
Technical Details:
- Attacker manipulated reward calculations through flash loans
- Vulnerability existed in custom reward logic
- Audit missed the specific attack vector
- No circuit breakers to prevent large drains
Protection Strategies:
- Avoid newly forked protocols without extensive testing
- Look for protocols with multiple audit rounds
- Consider insurance for experimental protocols
- Monitor protocol changes and upgrades
Cross-Chain Bridge Attack (2024)
What Happened: Hackers exploited a cross-chain bridge vulnerability. Affecting multiple lending protocols that relied on bridged assets.
Impact Analysis:
- $50+ million drained from bridge protocol
- Cascading effects on connected lending protocols
- Temporary freezing of cross-chain operations
- Market confidence impact across DeFi ecosystem
- Partial recovery through insurance claims
Risk Mitigation:
- Understand cross-chain dependencies
- Diversify across different blockchain ecosystems
- Monitor bridge security and TVL changes
- Consider native assets over bridged tokens
Quantitative Security Assessment Methodologies
Professional Risk Scoring Frameworks
Institutional investors. Professional traders employ sophisticated quantitative methodologies to assess crypto lending security risks. These frameworks combine multiple risk factors into comprehensive scoring systems that enable systematic comparison across different lending platforms and protocols.
Advanced risk assessment incorporates statistical analysis of historical exploit patterns, correlation analysis between different risk factors, and Monte Carlo simulations to model potential loss scenarios. Professional frameworks typically weight technical security (40%), operational security (25%), regulatory compliance (20%), and market risk factors (15%) to create composite risk scores.
Technical Security Metrics and Benchmarking
Professional security assessment utilises specific technical metrics including code coverage percentages (target > 95%), audit depth scores based on line-by-line review coverage, formal verification completion rates,. Bug bounty programme effectiveness measured by vulnerability discovery rates and resolution times.
Benchmarking against industry standards involves comparing platforms against established security frameworks such as NIST Cybersecurity Framework, ISO 27001 compliance levels, and SOC 2 Type II audit results. Leading platforms typically achieve 99.9%+ uptime, sub-24-hour incident response times,. Maintain comprehensive insurance coverage exceeding $100 million.
Operational Security Excellence Indicators
Institutional-grade operational security assessment examines multi-signature wallet implementations (typically requiring 3-of-5 or 4-of-7 signature thresholds), hardware security module (HSM) integration for key management,. Geographic distribution of operational infrastructure across multiple jurisdictions and data centres.
Advanced operational metrics include mean time to detection (MTTD) for security incidents (target <15 minutes), mean time to response (MTTR) for critical issues (target <1 hour),. Comprehensive disaster recovery capabilities with recovery time objectives (RTO) under 4 hours and recovery point objectives (RPO) under 15 minutes.
Regulatory Compliance and Legal Framework Analysis
Professional compliance assessment evaluates platforms against multiple regulatory frameworks including European Union's Markets in Crypto-Assets (MiCA) regulation, US Securities and Exchange Commission (SEC) guidance, and Financial Action Task Force (FATF) recommendations for virtual asset service providers.
Compliance scoring incorporates Know Your Customer (KYC) implementation depth, Anti-Money Laundering (AML) monitoring effectiveness, transaction reporting capabilities, and cross-border regulatory coordination. Leading platforms maintain licenses in multiple jurisdictions. Demonstrate proactive regulatory engagement with regular compliance audits and transparent reporting.
Advanced Threat modelling and Attack Vector Analysis
Sophisticated Attack Pattern Recognition
Professional security analysis employs advanced threat modelling techniques that map potential attack vectors across multiple dimensions including technical vulnerabilities, social engineering vectors, insider threats, and systemic market risks. These models incorporate game theory principles to predict attacker behaviour and optimal defensive strategies.
Attack vector analysis includes flash loan manipulation scenarios, oracle price feed attacks, governance token concentration risks, and cross-protocol composability exploits. Professional models assign probability distributions to different attack scenarios. Calculate expected loss values using historical exploit data and current market conditions.
Economic Security Analysis and Incentive Alignment
Advanced security assessment examines economic incentive structures that influence platform security such as validator reward mechanisms, penalty structures for malicious behaviour, and long-term sustainability of security budgets. Economic security analysis evaluates whether attack costs exceed potential rewards across different market conditions.
Incentive alignment assessment includes analysis of token distribution patterns, governance participation rates,. Alignment between platform success and stakeholder interests. Professional analysis examines whether economic incentives create sustainable security over multi-year time horizons. During various market stress scenarios.
Systemic Risk Assessment and Contagion Analysis
Institutional risk management incorporates systemic risk analysis that examines interconnections between different lending platforms, shared infrastructure dependencies,. Potential contagion effects during market stress events. This analysis includes correlation studies between platform failures and broader market conditions.
Contagion analysis models how failures in one protocol or platform might cascade through the broader DeFi ecosystem. Affecting multiple lending platforms simultaneously. Professional models incorporate network analysis techniques to identify critical nodes. Potential systemic vulnerabilities that could amplify individual platform risks.
Comprehensive Security Best Practices
Platform Selection Strategy
Tier 1: Established Platforms (40% allocation)
- CeFi Examples: Nexo, Binance Earn, Kraken
- DeFi Examples: Aave, Compound, MakerDAO
- Criteria: 3+ years operation, regulatory compliance, insurance coverage
- Risk Level: Low to moderate
Tier 2: Emerging Platforms (30% allocation)
- Examples: Newer regulated exchanges, audited DeFi protocols
- Criteria: 1-3 years of operation, good security practices. Growing TVL
- Risk Level: Moderate
Tier 3: Experimental (20% allocation)
- Examples: New DeFi protocols, innovative yield strategies
- Criteria: Audited code, insurance available, small position sizes
- Risk Level: High
Reserve Fund (10% allocation)
- Purpose: Emergency liquidity, opportunity fund
- Storage: Cold storage, stablecoins
- Access: Immediate availability
Operational Security Measures
Account Security
- Two-Factor Authentication: Use hardware keys (YubiKey) or authenticator apps
- Strong Passwords: Unique passwords for each platform
- Email Security: Separate email for crypto activities
- Device Security: Dedicated devices for crypto transactions
- Network Security: Avoid public WiFi for crypto activities
Wallet Security
- Hardware Wallets: Use for DeFi interactions and large amounts
- Multi-Signature: For large positions requiring multiple approvals
- Seed Phrase Security: Offline storage in multiple secure locations
- Regular Backups: Test recovery procedures periodically
- Address Verification: Always verify recipient addresses
Transaction Security
- Small Test Transactions: Test with small amounts first
- Contract Verification: Verify smart contract addresses
- Gas Fee Monitoring: Avoid suspicious high-fee transactions
- Slippage Settings: Use conservative slippage tolerances
- Transaction Timing: Avoid transactions during high volatility
Continuous Monitoring System
Platform Health Monitoring
- Daily Checks: Platform status, yield rates, news alerts
- Weekly Reviews: TVL changes, user sentiment, competitor analysis
- Monthly Audits: Portfolio allocation, risk assessment, rebalancing
- Quarterly Reviews: Strategy evaluation, platform comparison, goal adjustment
Risk Indicators to Monitor
- Yield Volatility: Sudden rate changes may indicate stress
- TVL Fluctuations: Large outflows suggest user concerns
- Social Sentiment: Community discussions and complaints
- Regulatory News: Changes affecting platform operations
- Market Conditions: Volatility affecting collateral values
Insurance and Protection Strategies
Available Insurance Options
CeFi Platform Insurance
- FDIC-Style Coverage: Some platforms offer deposit insurance up to $250,000
- Third-Party Insurance: Lloyd's of London. Other insurers cover custody risks
- Platform Reserves: Excess reserves to cover customer losses
- Coverage Scope: Typically covers theft and custody breaches, not insolvency
DeFi Insurance Protocols
- Nexus Mutual: Community-governed insurance for smart contract risks
- InsurAce: Multi-chain insurance with competitive pricing
- Unslashed Finance: Institutional-grade DeFi insurance
- Coverage Types: Smart contract exploits, oracle failures. Slashing events
When to Buy Insurance
| Position Size | Platform Type | Recommendation | Reasoning |
|---|---|---|---|
| Under $5,000 | Established CeFi/DeFi | Self-insure | Premium costs outweigh benefits |
| $5,000-$25,000 | Established platforms | Consider insurance | Evaluate cost vs. risk tolerance |
| $25,000+ | Any platform | Strongly recommend | Significant loss potential |
| Any amount | Experimental DeFi | Required | High exploit risk |
Regulatory Landscape and Compliance
Global Regulatory Framework
The regulatory environment for digital asset lending has evolved significantly. Providing clearer guidelines and enhanced consumer protections:
European Union - MiCA Regulation
- Implementation: Fully effective since January 2025
- Key Requirements: Licensing, capital requirements, segregation of funds
- Consumer Protection: Mandatory insurance, clear risk disclosures
- Impact: Higher compliance costs. But Improved platform safety
United States - Evolving Framework
- SEC Guidance: Clearer definitions of securities vs. commodities
- State Regulations: Money transmitter licenses required
- FDIC Considerations: Some platforms exploring deposit insurance
- Compliance Trends: Increased reporting and transparency requirements
Asia-Pacific Developments
- Singapore: Comprehensive DeFi regulation framework
- Japan: Enhanced custody and lending platform oversight
- Australia: Licensing requirements for crypto asset services
- Hong Kong: Professional investor focused regulations
Benefits of Regulatory Compliance
| Compliance Aspect | User Benefits | Platform Requirements | Risk Reduction |
|---|---|---|---|
| Licensing | Legal recourse, regulatory oversight | Capital requirements, governance standards | Reduces platform failure risk |
| Fund Segregation | Protected customer assets | Separate custody arrangements | Eliminates commingling risk |
| Reporting | Transparency, early warning signs | Regular financial disclosures | Improves market confidence |
| Insurance | Loss protection coverage | Third-party insurance policies | Mitigates custody and operational risks |
Advanced Security Technologies in Cryptocurrency Lending
Emerging Security Solutions
Multi-Party Computation (MPC)
MPC technology enables secure key management without single points of failure:
- Distributed Key Generation: No single entity holds complete private keys
- Threshold Signatures: Requires multiple parties to authorize transactions
- Platform Examples: Fireblocks, Curv (acquired by PayPal), Sepior
- Benefits: Eliminates single points of failure, maintains operational efficiency
- Adoption: 60% of institutional platforms now use MPC technology
Zero-Knowledge Proofs in Lending
ZK technology enables privacy-preserving verification of platform solvency:
- Proof of Reserves: Verify platform holdings without revealing addresses
- Privacy Protection: Maintain user confidentiality while proving solvency
- Real-time Verification: Continuous proof generation and verification
- Implementation Examples: Kraken's ZK proof of reserves, Binance's ZK audits
AI-Powered Risk Management
Machine learning enhances platform security and risk assessment:
- Fraud Detection: Real-time analysis of suspicious transaction patterns
- Credit Risk Assessment: Dynamic evaluation of borrower creditworthiness
- Market Risk Monitoring: Predictive models for volatility and liquidation risks
- Operational Risk: Automated monitoring of platform health indicators
Security Performance Metrics
| Security Metric | Industry Average | Top Tier Platforms | Improvement (YoY) |
|---|---|---|---|
| Security Incident Rate | 2.3 per 1000 platforms | 0.8 per 1000 platforms | -45% |
| Average Recovery Time | 72 hours | 24 hours | -33% |
| Insurance Coverage Rate | 65% of platforms | 95% of platforms | +28% |
| Audit Frequency | Bi-annual | Quarterly | +100% |
| User Fund Recovery Rate | 78% | 94% | +15% |
Security Recommendations by User Type
The Future of Cryptocurrency Lending Security
Emerging Security Trends
Institutional-Grade Infrastructure
The digital asset lending sector is rapidly adopting traditional finance security standards:
- Bank-Level Custody: Integration with traditional custodians like State Street and BNY Mellon
- Regulatory Sandboxes: Controlled environments for testing new lending products
- Central Bank Digital Currencies (CBDCs): Government-backed digital currencies reducing counterparty risk
- Traditional Insurance: Major insurers like AXA and Allianz entering crypto coverage
Advanced Risk Management
Next-generation risk management systems are being deployed:
- Real-Time Stress Testing: Continuous evaluation of portfolio resilience
- Cross-Platform Risk Aggregation: Holistic view of user exposure across platforms
- Predictive Analytics: AI models predicting platform failures and market stress
- Dynamic Collateralization: Automated adjustment of collateral requirements
Interoperability and Standards
Industry-wide security standards are emerging:
- Security Certification Programs: standardised security assessments for platforms
- Cross-Chain Security Protocols: Unified security frameworks across blockchains
- Industry Insurance Pools: Shared insurance funds for systemic risk protection
- Regulatory Harmonization: Aligned global standards for digital asset lending
Security Roadmap:-2027
2025: Foundation Year
- Full MiCA implementation across EU
- US regulatory clarity on lending products
- Widespread adoption of MPC technology
- Insurance coverage becomes standard
2026: Innovation Year
- Zero-knowledge proof of reserves becomes standard
- AI-powered risk management deployment
- Cross-chain security protocol maturation
- Institutional custody integration
2027: Maturation Year
- Global regulatory harmonization
- Industry-wide security certification
- CBDC integration with lending platforms
- Quantum-resistant security implementation
Investment Strategy Implications
These security improvements will reshape digital asset lending investment strategies:
Short-Term (2025)
- Platform Selection: prioritise regulated, insured platforms
- Diversification: Spread risk across 5-8 platforms maximum
- Due Diligence: Enhanced security assessment becomes critical
- Insurance: Consider coverage for positions over $10,000
Medium-Term (2026-2027)
- Institutional Platforms: Shift towards bank-grade custody solutions
- Automated Risk Management: Leverage AI-powered portfolio optimisation
- Cross-Chain Strategies: Diversify across multiple blockchain ecosystems
- Regulatory Arbitrage: optimise across different regulatory jurisdictions
Long-Term (2027+)
- CBDC Integration: Incorporate government-backed digital currencies
- Quantum-Safe Protocols: Transition to quantum-resistant platforms
- Global Standards: Benefit from harmonized international regulations
- Mature Market: Enjoy lower risk premiums and stable yields
Worked Security Assessment: Scoring a Platform Before You Deposit
Here is a practical framework you can apply to any lending platform in under 30 minutes. Score each category from 0-10, then calculate a weighted total. Any platform scoring below 50/100 should be avoided entirely.
Step 1: Audit and Code Security (30% weight)
Check whether the platform has been audited by at least two independent firms from this tier-one list: Trail of Bits, OpenZeppelin, Consensys Diligence, Certora, or Halborn. A single audit from a lesser-known firm scores 3/10. Two tier-one audits with no critical findings scores 8/10. Aave scores 9/10 (audited by Trail of Bits, OpenZeppelin, Certora, plus formal verification). Compound scores 8/10. A newly launched fork with one audit from an unknown firm scores 2/10.
Step 2: Track Record and Incident History (25% weight)
How long has the platform operated without losing user funds? Score: 0-6 months = 2/10, 6-12 months = 4/10, 1-3 years = 6/10, 3+ years with no major exploit = 8/10, 5+ years = 10/10. Deduct 3 points for any incident involving user fund loss, 1 point for incidents that were contained without losses. Aave: 10/10 (5+ years, zero exploits on mainnet). Euler: 4/10 (operational since 2021 but suffered a $197M exploit in March 2023, subsequently recovered).
Step 3: Financial Transparency (20% weight)
Does the platform publish proof of reserves? For CeFi: real-time Armanino-style attestations score 9/10. Quarterly PDF reports score 5/10. No proof of reserves scores 0/10. For DeFi: fully on-chain and verifiable via DefiLlama scores 10/10 automatically. Nexo scores 9/10 (real-time Armanino attestations). A CeFi platform publishing only annual reports scores 3/10.
Step 4: Insurance and Backstop (15% weight)
What protects you if something goes wrong? Nexo: $775M custodial insurance through Lloyd's (8/10). Aave: $400M+ Safety Module in staked AAVE tokens (7/10). A platform with no insurance and no safety fund scores 0/10. If the insurance covers only custody theft (not insolvency), deduct 2 points. If DeFi insurance via Nexus Mutual is available for the protocol, add 1 point.
Step 5: Regulatory Status (10% weight)
Licensed in major jurisdictions (EU, US, UK, Singapore) scores 8-10/10. Licensed in one minor jurisdiction scores 4/10. Unlicensed scores 0/10. Nexo: 9/10 (EU, UK, multiple US states). Aave: 5/10 (DeFi protocol, no licensing required but limited legal recourse). An offshore CeFi platform with no licences: 0/10.
Example: Scoring Aave vs an Unknown CeFi Platform
Aave: Audit 9 x 0.30 = 2.7, Track Record 10 x 0.25 = 2.5, Transparency 10 x 0.20 = 2.0, Insurance 7 x 0.15 = 1.05, Regulatory 5 x 0.10 = 0.5. Total: 87.5/100. A hypothetical unlicensed CeFi platform offering 15% APY with one audit and no proof of reserves: Audit 3 x 0.30 = 0.9, Track Record 4 x 0.25 = 1.0, Transparency 0 x 0.20 = 0, Insurance 0 x 0.15 = 0, Regulatory 0 x 0.10 = 0. Total: 19/100. The numbers make the decision obvious.
Conclusion
Crypto lending security has improved materially since 2022, but the risks have not disappeared -- they have shifted. Platform insolvency risk is lower thanks to MiCA and proof-of-reserves requirements, but smart contract exploits still drained $1.7 billion from DeFi protocols in 2024 alone. The question is not "is crypto lending safe?" but "can you identify and manage the specific risks of your chosen platform?"
The practical answer: use the five-point scoring framework above before depositing on any platform. Diversify across at least two platforms (one CeFi, one DeFi) so that a single failure does not wipe you out. Keep your total crypto lending exposure below 20% of your overall portfolio. Buy DeFi insurance (Nexus Mutual, InsurAce) for any positions above 10,000 pounds on protocols that are less than three years old. For established platforms like Aave (5+ years, zero mainnet exploits) or Nexo (6+ years, never froze withdrawals), the risk-reward ratio favours participation with appropriately conservative position sizes.
If a platform offers yields significantly above market rates (15%+ on stablecoins in 2025), treat it as a red flag, not an opportunity. Celsius offered 18% and went bankrupt. The platforms that survived the 2022 wipeout are the ones that offered sustainable yields backed by real borrowing demand. That lesson cost the industry $20 billion. Do not let it cost you personally.
For UK-based lenders, tax treatment adds another consideration. HMRC treats lending yield as taxable income at the point you receive it, valued in GBP at the market price on that date. If you are lending across multiple protocols and chains, each reward claim creates a separate income tax event. Use crypto tax software (Koinly, CryptoTaxCalculator) from day one to track these automatically — retroactive reconstruction of DeFi lending transactions across multiple wallets and chains is extremely time-consuming and error-prone.
Sources & References
- DeFi Pulse. (2025). "Total Value Locked (TVL) in DeFi". DeFi Pulse provides real-time analytics on DeFi protocol security and TVL metrics.
- Chainalysis. (2025). "Crypto Crime Report 2025". Comprehensive analysis of security incidents, hacks,. Fraud in crypto lending platforms.
- CoinDesk. (2025). "What Is DeFi?". Educational resource on decentralised finance security and best practices.
Frequently Asked Questions
- What are the main security risks of crypto lending in 2025?
- Main risks include platform insolvency (custody risk), smart contract exploits in DeFi protocols, liquidity freezes during market stress, regulatory actions affecting operations, counterparty defaults, and cybersecurity breaches. CeFi platforms face custody risk, while DeFi protocols face code vulnerabilities and oracle manipulation risks.
- Is DeFi lending more secure than CeFi lending?
- Neither is universally more secure - they have different risk profiles. DeFi eliminates custody risk. Provides transparency. But Introduces smart contract vulnerabilities and complexity. CeFi offers simplicity, customer support, and sometimes insurance,. But This depends on the platform's solvency and proper governance. The best approach often combines both with proper diversification.
- How can I evaluate the security of a crypto lending platform?
- For CeFi platforms, check regulatory licensing, financial audits, insurance coverage, team background, and user reviews. For DeFi protocols, examine smart contract audits, bug bounty programs, TVL stability, governance structure, and operational history. Look for transparency in operations, proof of reserves, and clear risk disclosures.
- What security measures should I take when using digital asset lending?
- Diversify across multiple platforms (never more than 20% on one platform), use hardware wallets for DeFi, enable 2FA on all accounts, start with small amounts, verify platform legitimacy, avoid suspicious high yields, maintain emergency funds outside lending,. Regularly monitor your positions and platform health.
- Should I buy insurance for my digital asset lending positions?
- Insurance is recommended for positions over $10,000 or when using experimental protocols. For smaller amounts on established platforms, self-insurance may be a more cost-effective option. DeFi insurance typically costs 3-6% annually and covers 60-80% of losses from specific events, such as smart contract exploits,. But Excludes platform insolvency and market losses.
- What are the warning signs of an unsafe lending platform?
- Red flags include: unsustainable yields (20%+ on stablecoins), lack of regulatory compliance, no security audits, poor customer service, withdrawal delays, lack of transparency about fund usage, anonymous teams, negative user reviews, and recent security incidents. Always research thoroughly before depositing funds.
How has digital asset lending security improved since 2022?
Security has improved through clearer regulations (EU MiCA), better insurance options, mandatory proof-of-reserves, improved audit standards, better risk management practices, enhanced user education,. Lessons learnt from major platform failures like Celsius and FTX. However, risks remain,. Proper due diligence is still essential.
What should I do if my lending platform gets hacked or fails?
Immediately document all positions and communications, attempt to withdraw remaining funds if possible, file insurance claims if applicable, join user recovery groups, seek legal consultation for significant losses,. Participate in bankruptcy proceedings. Quick action in the first 24-48 hours is crucial for maximising recovery chances.
How do I assess the security of a new DeFi lending protocol?
Check for multiple independent audits from reputable firms (Consensys Diligence, Trail of Bits, OpenZeppelin), review the audit reports for critical findings, verify the protocol has been live for at least 3-6 months, examine the TVL growth and stability, check for active bug bounty programs,. Review the governance structure and token distribution.
What are the latest security innovations in digital asset lending?
Recent innovations include Multi-Party Computation (MPC) for distributed key management, zero-knowledge proofs for privacy-preserving solvency verification, AI-powered fraud detection, real-time risk monitoring systems, automated circuit breakers, and cross-chain security protocols. These technologies significantly enhance platform security and user protection.
How has regulatory compliance improved digital asset lending security?
Regulatory compliance has introduced mandatory fund segregation, capital requirements, regular audits, insurance requirements, and clear governance standards. The EU's MiCA regulation and evolving US frameworks have forced platforms to adopt institutional-grade security practices, significantly reducing the risk of platform failures and improving user protections.
Should I use centralised or decentralised lending platforms for better security?
The optimal approach is diversification across both. CeFi platforms offer regulatory protection, insurance,. Professional management. But Carry custody risk. DeFi protocols provide transparency and self-custody. But Have smart contract risks. A balanced portfolio might allocate 60% to regulated CeFi platforms and 40% to audited DeFi protocols. Depending on your risk tolerance.
← Back to Crypto Investing Blog Index
Financial Disclaimer
This content is not financial advice. All information provided is for educational purposes only. Cryptocurrency investments carry significant investment risk, and past performance does not guarantee future results. Always do your own research and consult a qualified financial advisor before making investment decisions.