Hardware Wallet Security: Complete Guide

Hardware wallets isolate your private keys from internet-connected devices — the single most effective step you can take to protect cryptocurrency holdings. This guide covers how they work, compares four fundamentally different security architectures (Ledger, Trezor, Keystone, Tangem), and helps you choose the right one for your situation.
Introduction
A hardware wallet is a physical device that stores your cryptocurrency private keys offline, isolated from internet-connected computers and phones. This isolation — known as cold storage — eliminates the most common and most damaging attack vector in cryptocurrency: remote theft through malware, phishing, compromised exchanges, or man-in-the-middle attacks. If your keys never touch an online device, they cannot be stolen remotely — regardless of how sophisticated the malware or how compromised your computer may be. Hardware wallets cost $60–280 depending on the model and manufacturer, and protect holdings of any size, though they become essential once your portfolio exceeds $1,000–5,000.
Four fundamentally different security architectures dominate the hardware wallet market in 2026. Ledger uses a dual-chip design with an EAL5+ certified secure element and connects via USB or Bluetooth. Trezor prioritises open-source transparency — every line of firmware code is auditable on GitHub — and connects via USB only. Keystone takes air-gap isolation to its logical extreme: no USB, no Bluetooth, no WiFi — all communication happens through QR codes scanned by the device's camera. Tangem eliminates the seed phrase entirely — your keys live on an NFC card that you tap to sign transactions, with backup via cloned cards.
Each architecture makes a different tradeoff between security, convenience, and complexity. No single wallet is "best" — the right choice depends on what you hold, how often you transact, and how much setup friction you are willing to accept. A Bitcoin maximalist running a multisig setup with Trezor and Sparrow has fundamentally different requirements than a DeFi power user signing 20 transactions per day on Ethereum through MetaMask with a Ledger. A non-technical user gifting crypto to a family member needs a different solution than an institutional treasury manager securing $10 million across geographically separated signers.
We have tested all four devices hands-on — setup timing, transaction signing, DeFi integration, and recovery procedures. Ledger took 8 minutes from unboxing to first signed transaction. Trezor took 10 minutes. Keystone took 25 minutes due to the QR code learning curve. Tangem took 3 minutes — the fastest hardware wallet setup we have encountered. These real-world timings matter because setup friction directly affects whether you will actually use the device or leave it in a drawer.
This guide synthesises those findings into a practical decision framework. You will learn how hardware wallets isolate your keys, what differentiates each of the four security architectures, how to set up your device properly (including seed phrase storage, passphrase protection, and multisig for larger holdings), which attack vectors you should understand and defend against, and how to use hardware wallets safely with DeFi protocols through MetaMask and WalletConnect. Whether you hold $1,000 in Bitcoin or manage a six-figure multi-chain portfolio, the right hardware wallet — configured correctly — is the most cost-effective security investment you can make in crypto.
If you already know which wallet you want, jump to our individual reviews for Ledger, Trezor, Keystone, or Tangem linked in each section below. If you want to compare two specific devices, see Trezor vs Ledger or Ledger vs Tangem. Ready to buy? See our Ledger, Tangem, and Keystone referral guides for exclusive offers.
How Hardware Wallets Work
Private Key Isolation
Your cryptocurrency exists on the blockchain, not inside any device. What a hardware wallet stores is the private key — a 256-bit number that proves ownership and authorises transactions. Whoever holds this key controls the funds. The core security principle of hardware wallets is simple: the private key is generated on the device, stored on the device, and used for signing on the device. It never leaves.
When you use a software wallet on your phone or computer, your private key exists in memory on an internet-connected device. Malware, keyloggers, clipboard hijackers, and remote access trojans can all extract it. A hardware wallet eliminates this entire attack surface by keeping the key in a physically separate, purpose-built device that has no general-purpose operating system for malware to exploit.
Why should you care about this distinction? Because the difference between a hot wallet and a hardware wallet is the difference between leaving your house keys under the doormat and keeping them in a vault. If you hold more than $1,000 in crypto on a software wallet right now, you should seriously consider moving those funds to a hardware wallet within the next week. The cost of a basic device ($55–79) is trivial compared to the potential loss from a single malware infection on your computer or phone.
The Signing Process
Every cryptocurrency transaction requires a digital signature — mathematical proof that the owner of the private key authorised the transfer. Here is how signing works with a hardware wallet:
- Step 1: You create a transaction on your computer or phone (e.g. "send 0.5 ETH to address 0xABC...")
- Step 2: The unsigned transaction is sent to the hardware wallet — via USB cable (Ledger, Trezor), Bluetooth (Ledger), or QR code (Keystone)
- Step 3: The hardware wallet displays the transaction details on its own screen — recipient address, amount, and fees — for you to verify
- Step 4: You confirm by pressing a physical button or scanning your fingerprint on the device
- Step 5: The device signs the transaction internally using the private key, then sends the signed transaction back to your computer
- Step 6: Your computer broadcasts the signed transaction to the blockchain network
The critical point: at no stage does the private key leave the hardware wallet. The device receives unsigned data, performs the cryptographic signing internally, and outputs only the signed result. Even if your computer is completely compromised by malware, the attacker cannot extract your key — they can only see the signed transaction that was already authorised.
Seed Phrases and Recovery
During initial setup, every hardware wallet (except Tangem) generates a seed phrase — a sequence of 12 or 24 English words derived from the BIP39 standard. This phrase is a human-readable encoding of the master private key from which all your wallet addresses are mathematically derived using a system called Hierarchical Deterministic (HD) wallets (BIP32/BIP44).
Your seed phrase is the ultimate backup. If your hardware wallet is lost, stolen, or destroyed, you can enter the seed phrase into a new device and restore complete access to all your funds across all blockchain networks. This also means that anyone who obtains your seed phrase controls your crypto — securing this phrase is the single most important security step you will take.
Tangem takes a different approach: no seed phrase exists at all. The private key is generated inside the NFC chip during manufacturing and cannot be extracted by any means — including by Tangem themselves. Backup is achieved by cloning the key onto 2–3 additional Tangem cards during setup. This eliminates the risk of seed phrase theft but means recovery depends entirely on having a backup card available.
What Hardware Wallets Cannot Protect Against
Hardware wallets protect your private keys, but they do not protect you from signing a malicious transaction. If a compromised DApp presents a transaction that drains your wallet and you approve it on your device screen without reading the details, the hardware wallet will faithfully sign it. You are the last line of defence — always verify the recipient address, amount, and contract interaction on the device screen before confirming.
Here is a practical rule you should follow: before you confirm any transaction on your hardware wallet, ask yourself three questions. First, does the recipient address on the device screen match what you intended? Second, is the amount correct — not orders of magnitude higher than expected? Third, do you understand what contract you are interacting with? If you cannot answer yes to all three, reject the transaction and investigate. This 10-second habit can save you from the most common hardware wallet user error — approving a transaction you did not fully understand.

Four Security Architectures Compared
Secure Element + USB/Bluetooth (Ledger)
Ledger devices use a dual-chip architecture: an EAL5+ certified secure element (the same type of chip used in bank cards and passports) handles all cryptographic operations, while a separate general-purpose microcontroller manages the user interface and communication. Private keys are generated and stored inside the secure element and cannot be extracted — even if an attacker has physical access to the device and disassembles it.
Ledger connects to your computer via USB-C and to your phone via Bluetooth (Nano X and Stax models). The Bluetooth connection is encrypted and the signing still happens on the secure element, but Bluetooth does introduce a wireless attack surface that purely wired or air-gapped devices avoid. Ledger's firmware is proprietary and not open source, which means you must trust Ledger's security team and their third-party auditors rather than verifying the code yourself.
In our testing, Ledger setup took 8 minutes. The Ledger Live companion app supports 5,500+ tokens and provides the widest app ecosystem of any hardware wallet. If you need mobile DeFi signing via Bluetooth or the broadest altcoin support, Ledger is the pragmatic choice. You should consider Ledger if your portfolio spans more than 3–4 different chains and you want a single device that can manage all of them through one companion app. Price range: $79 (Nano S Plus) to $279 (Stax).
Open-Source + USB (Trezor)
Trezor was the first hardware wallet (launched 2014) and takes a fundamentally different approach to trust: instead of relying on a proprietary secure element, Trezor's entire firmware is open source and auditable on GitHub. Any security researcher can review the code, compile it from source, and verify that the binary running on the device matches the published source code. This transparency is Trezor's core value proposition.
The tradeoff is that Trezor devices do not contain a dedicated secure element chip. Key storage relies on the general-purpose microcontroller with software-level encryption. Physical attacks (requiring direct access and specialised equipment) are theoretically easier against Trezor than against Ledger's EAL5+ chip, though no practical remote exploits have been demonstrated in 12 years of operation. Trezor connects via USB only — no Bluetooth or wireless, which reduces the attack surface.
Trezor setup took 10 minutes in our testing. The Model One ($69) is the most affordable entry point into hardware wallet security. The Model T ($219) adds a colour touchscreen for secure PIN and passphrase entry directly on the device. Shamir Backup support lets you split your recovery phrase into multiple shares, eliminating the single point of failure of a standard seed phrase. For Bitcoin maximalists and open-source advocates, Trezor's integration with Sparrow and Electrum wallets provides coin control, UTXO management, and CoinJoin support that Ledger Live does not offer.
Air-Gap + QR Code (Keystone)
Keystone eliminates all physical and wireless connections entirely. The device has no USB port (charging only via USB-C, with no data transfer), no Bluetooth, no WiFi, and no NFC. All communication between your phone or computer and the Keystone device happens through QR codes: the unsigned transaction is displayed as a QR code on your screen, Keystone's camera scans it, signs the transaction offline, and displays the signed result as a QR code for your phone to scan back.
This air-gap architecture provides the strongest isolation available in a consumer hardware wallet. Since the device never physically or wirelessly connects to any other device, entire categories of attack vectors — malicious USB cables, Bluetooth eavesdropping, BadUSB firmware attacks — are eliminated by design. Keystone's firmware is open source, and the device includes an EAL5+ secure element for key storage, combining both Trezor's transparency and Ledger's hardware security.
The tradeoff is friction. In our testing, initial setup took 25 minutes (vs 8 for Ledger), and each transaction requires a scan-sign-scan QR cycle that takes 30–45 seconds — roughly 3x slower than plugging in a USB device. The 4-inch touchscreen is the best display in the hardware wallet market, making transaction verification significantly easier than on Ledger's or Trezor's smaller screens. Price: $119 (Essential) to $169 (Pro 3).
NFC Seedless Card (Tangem)
Tangem abandons the entire seed phrase model. The private key is generated inside a secure NFC chip during manufacturing and can never be extracted — not by you, not by Tangem, not by an attacker with physical access. You sign transactions by tapping the card against your phone's NFC reader. There is no screen on the device, no battery, and no buttons. Transaction verification happens on your phone screen, and signing happens inside the card's chip.
Backup works by cloning the private key onto 2–3 additional Tangem cards during initial setup. If you lose your primary card, any backup card provides full access. This eliminates the most common cause of crypto loss: forgotten, damaged, or stolen seed phrases. However, if you lose all your cards and have no backup, your funds are permanently inaccessible — there is no recovery phrase to fall back on.
Tangem is the simplest hardware wallet we have tested: setup took 3 minutes, and transactions require a single NFC tap. The card is credit-card sized, waterproof, and has a 25-year battery life (for the NFC chip's passive operation). It supports 6,000+ tokens across multiple chains. The lack of a device screen means you must trust your phone to display accurate transaction details — a weaker verification model than devices with dedicated screens. If you are buying your first hardware wallet or recommending one to a friend who finds technology intimidating, you should start with Tangem — you can always add a screen-equipped device later as your comfort level grows. Price: $55–70 for a 3-card set.
| Feature | Ledger | Trezor | Keystone | Tangem |
|---|---|---|---|---|
| Security Model | EAL5+ secure element | Open-source firmware | Air-gap + secure element | NFC chip, seedless |
| Connection | USB-C, Bluetooth | USB only | QR code only | NFC tap |
| Seed Phrase | 24 words | 12 or 24 words | 12 or 24 words | None (card backup) |
| Open Source | No (proprietary) | Yes (full) | Yes (full) | Partial |
| Device Screen | Small (Nano) / Large (Stax) | Small (One) / Touch (T) | 4-inch touchscreen | None |
| Setup Time | 8 minutes | 10 minutes | 25 minutes | 3 minutes |
| Price Range | $79–$279 | $69–$219 | $119–$169 | $55–$70 |
| Best For | Widest ecosystem | Open-source advocates | Maximum security | Simplicity, no seed |
Choosing the Right Hardware Wallet
By Use Case
Bitcoin-only storage: Trezor paired with Sparrow or Electrum wallet. These specialist wallets provide coin control, UTXO management, and CoinJoin privacy that Ledger Live does not support. Trezor's open-source firmware aligns with the Bitcoin community's verify-don't-trust philosophy.
Multi-chain DeFi: Ledger is the pragmatic choice — Ledger Live supports 5,500+ tokens and integrates directly with MetaMask for Ethereum, Polygon, Arbitrum, and other EVM chains. If you want air-gap security for DeFi, Keystone works with MetaMask and 100+ DApps via WalletConnect, though the QR signing workflow adds 30–45 seconds per transaction.
Simplicity above all else: Tangem eliminates seed phrase management entirely. If the person you are recommending a hardware wallet to would struggle with writing down and securing 24 words, Tangem's NFC card design removes that failure point. Setup takes 3 minutes.
Maximum security: Keystone's air-gap architecture provides the strongest isolation. No physical or wireless connection to any device, ever. For large holdings or institutional setups requiring multisig across geographically separated signers, Keystone's QR-based partial signature export is purpose-built for this workflow.
By Portfolio Size
Under $1,000: A reputable exchange with 2FA is adequate. The cost and complexity of a hardware wallet may not be justified at this level.
$1,000–$10,000: An entry-level hardware wallet makes sense. Trezor Model One ($69) or a Tangem 3-card set ($55–70) provide genuine cold storage at minimal cost. The device cost is 1–7% of your holdings — a reasonable insurance premium.
$10,000–$100,000: Invest in a premium device. Ledger Nano X ($79) or Keystone Essential ($119) provide stronger security features. At this level, you should also implement passphrase protection (creates a hidden wallet behind a secondary password) and consider a metal seed phrase backup plate ($25–50).
Over $100,000: Consider multisig — requiring 2-of-3 or 3-of-5 devices to authorise any transaction. This eliminates single-device failure as a risk. Keystone natively supports multisig coordination. Trezor and Ledger work with multisig through specialist software like Sparrow, Electrum, or Caravan.
By Technical Comfort
Non-technical users: Tangem (no seed phrase, tap to sign) or Ledger Nano S Plus (guided setup via Ledger Live app). Both minimise the number of decisions and technical concepts you need to understand.
Intermediate users: Ledger Nano X (Bluetooth convenience, broad ecosystem) or Trezor Model T (touchscreen, Shamir Backup option). Both provide a good balance of security and usability.
Advanced users: Keystone Pro 3 (air-gap, open-source, multisig) or Trezor with Sparrow wallet (full coin control, CoinJoin, custom derivation paths). These setups require more initial learning but provide maximum control over your security posture.
Common Mistakes When Choosing
The most frequent mistake is buying the most expensive device when a simpler one would serve you better. If you hold only Bitcoin and Ethereum and never use DeFi, a Trezor Model One at $69 provides the same core security as a Ledger Stax at $279 — the premium buys you a larger screen and wireless charging, not stronger key isolation.
The second mistake is choosing based on token count alone. If you hold assets across 15 different chains, Ledger's 5,500+ token support matters. If you hold BTC and ETH only, every hardware wallet on the market supports both. Pay for the security architecture and convenience features you actually need, not for theoretical future compatibility with chains you may never use.
The third mistake is neglecting the ecosystem. A hardware wallet is only as useful as the software it integrates with. Ledger Live provides a full portfolio management experience. Trezor Suite is functional but more basic. Keystone relies on third-party wallets (MetaMask, Sparrow) for all management. Tangem's companion app handles everything but lacks advanced features. Before purchasing, verify that the device supports the specific DApps, chains, and workflows you use daily.
Setup Best Practices
Seed Phrase Storage
Your seed phrase is the master key to all your funds. How you store it determines whether you can recover from device loss — and whether an attacker can steal from you. Follow three rules: store it offline, store it in multiple locations, and never store it digitally.
- Write it on paper — use the card included with your device or plain paper. Write clearly in permanent ink. Store in a fireproof safe or safety deposit box.
- Consider a metal backup — steel plates like Cryptosteel or Billfodl survive fire (up to 1,200C) and water damage that would destroy paper. Cost: $25–70. Worth it for holdings above $5,000.
- Store in two physically separate locations — your home and a trusted family member's home, or a safety deposit box. If one location is compromised (fire, theft, flood), you still have a backup.
- Never photograph, email, or type your seed phrase — any digital copy can be extracted by malware, cloud sync, or a compromised device. If your phone automatically backs up photos to iCloud or Google Photos, a screenshot of your seed phrase is stored on a server you do not control.
Passphrase Protection
A passphrase (sometimes called the "25th word") is an optional secondary password that creates a mathematically separate hidden wallet from the same seed phrase. If someone obtains your 24 words but not your passphrase, they access only the base wallet — which you can keep empty or hold a small decoy amount. Your real holdings are in the passphrase-protected wallet that is invisible without the correct passphrase.
Passphrases are case-sensitive and include spaces and special characters. "MyPass123" and "mypass123" generate entirely different wallets. If you forget your passphrase, the funds in that wallet are permanently inaccessible. Write your passphrase down and store it separately from your seed phrase — ideally in a different physical location. Trezor and Keystone both support passphrases; Ledger supports them through advanced settings; Tangem does not use passphrases (no seed phrase model).
Multisig for Larger Holdings
Multisignature (multisig) setups require multiple devices to authorise a transaction — typically 2-of-3 or 3-of-5 configurations. This means no single device loss, theft, or compromise can result in fund loss. A 2-of-3 setup uses three hardware wallets stored in different locations; any two must sign to move funds.
Multisig adds complexity to every transaction but dramatically reduces single-point-of-failure risk. It is worth considering for holdings above $100,000 or for business treasuries. Keystone natively supports multisig with QR-based partial signature export. Trezor and Ledger work with multisig through Sparrow, Electrum, or dedicated tools like Caravan and Nunchuk.
Firmware Verification
Before trusting a new hardware wallet with your funds, verify that the firmware is genuine. Each manufacturer provides a different verification method:
- Ledger: Ledger Live performs an automatic genuineness check on first connection. The device's secure element contains a certificate that Ledger Live verifies against Ledger's servers.
- Trezor: You can compile the firmware from the open-source repository and compare the binary hash against what is running on your device. Trezor Suite also performs automatic verification.
- Keystone: Firmware binaries are published on GitHub with checksums. The device displays its firmware version and hash, which you can compare against the published values.
- Tangem: The NFC chip includes a manufacturer certificate that the Tangem app verifies automatically during first setup.
Metal Seed Phrase Backups
Paper backups are vulnerable to fire, water, and degradation over time. If you store more than $5,000 in crypto, invest $25–70 in a metal seed phrase backup plate. These are stainless steel or titanium plates where you stamp, engrave, or slide in letter tiles to record your 12 or 24 words. Quality options include Cryptosteel Capsule (letter tiles, $79), Billfodl ($55, letter tiles), and Blockplate (centre-punch steel, $30).
Metal backups survive house fires (steel melts at 1,370C, far above typical house fire temperatures of 600–800C), flooding, and decades of storage without degradation. Store your metal backup in a fireproof safe, safety deposit box, or with a trusted family member in a different building than your primary residence. If you use Shamir Backup (Trezor Model T), you need separate metal backups for each share, stored in different locations.
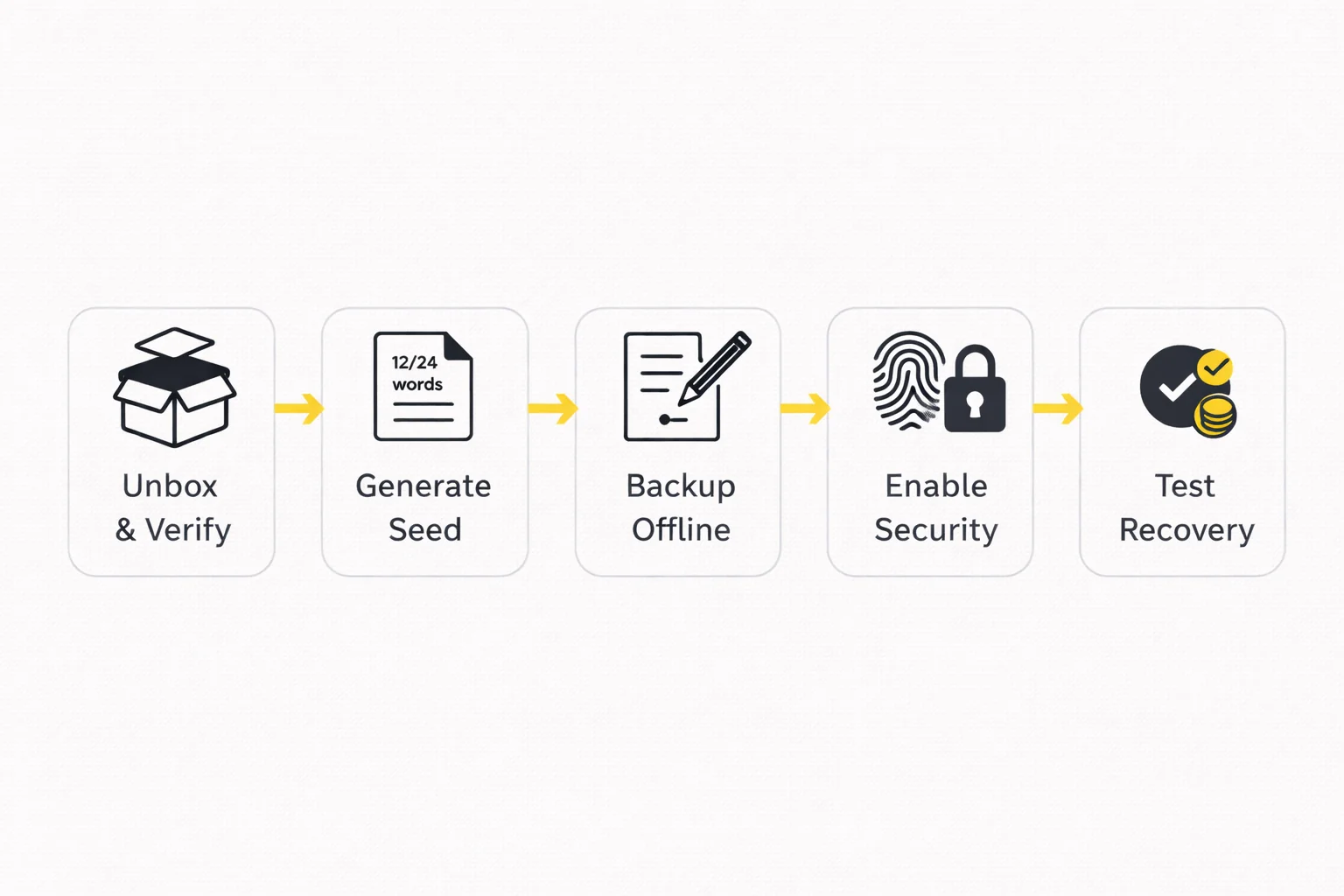
Your First Week with a Hardware Wallet
Day 1: Unbox the device, verify tamper-evident seals, and complete initial setup. Generate your seed phrase, write it down carefully, and enable all security features (PIN, biometrics, anti-phishing code where available). Do not deposit any funds yet.
Day 2: Order a metal backup plate if you do not already have one. While waiting for delivery, store your paper seed phrase in a secure temporary location. Connect your hardware wallet to its companion app (Ledger Live, Trezor Suite, or Tangem app) and familiarise yourself with the interface.
Day 3–4: Transfer your metal seed phrase to the metal backup when it arrives. Test the recovery process: reset the device, restore from your seed phrase, and verify the same addresses appear. Send a small test amount ($10–50) and verify it arrives correctly.
Day 5–7: Transfer your main holdings from exchanges to the hardware wallet in batches. Start with the largest holding, verify it arrives, then transfer the rest. If you use DeFi, connect your hardware wallet to MetaMask and test signing a small transaction through a DApp you frequently use. By the end of the week, all your holdings above $1,000 should be in hardware wallet custody.
Test Recovery Before Depositing
Before sending significant funds to your new hardware wallet, test the recovery process. Reset the device, restore from your seed phrase, and verify that the same addresses appear. This confirms that you wrote the seed phrase correctly and that recovery works. In our testing, full recovery took 30 seconds on TrustWallet, 2 minutes on Ledger, 3 minutes on Trezor, and 5 minutes on Keystone (QR re-pairing). Do this test with a small amount ($10–50) before transferring your main holdings. The 5 minutes this takes could save you from permanent fund loss if you made an error writing down your seed phrase. We consider this step mandatory, not optional — every hardware wallet setup guide that skips it is doing you a disservice.
Common Attack Vectors and How to Defend Against Them
The vast majority of hardware wallet losses come from social engineering and user error — not from hardware exploits. Understanding these attack vectors helps you defend against them.
Supply Chain Attacks
An attacker sells a pre-configured device with a known seed phrase, waits for you to deposit funds, then drains the wallet. This has happened with devices sold on Amazon, eBay, and other third-party marketplaces.
Defence: Buy only from the manufacturer's official website or authorised resellers listed on their site. Verify tamper-evident packaging is intact. During setup, always generate a new seed phrase on the device — never use a pre-printed phrase included in the box. If a device arrives with a seed phrase already written down, it is compromised.
Phishing and Social Engineering
Fake websites mimicking Ledger Live, Trezor Suite, or MetaMask ask you to enter your seed phrase "for verification" or "to fix a sync error." Fake customer support accounts on Twitter, Telegram, and Discord offer "help" that requires sharing your recovery words. This is the most common attack vector and accounts for the majority of hardware wallet losses.
Defence: Your seed phrase is never needed for normal operation — only for recovery on a new device. No legitimate support agent will ever ask for it. Bookmark official URLs (ledger.com, trezor.io, keyst.one) and never follow links from emails or social media messages. If someone asks for your seed phrase for any reason, it is a scam.
Firmware and Software Attacks
Malicious firmware updates or compromised companion apps could theoretically extract keys or alter transaction details. In 2023, a supply chain attack on Ledger's Connect Kit library briefly allowed attackers to inject malicious code into DApps that prompted Ledger users to sign draining transactions.
Defence: Only update firmware through official apps (Ledger Live, Trezor Suite). For Trezor and Keystone, open-source firmware means security researchers can audit updates before you install them. Always verify the transaction details on your device's screen, not on your computer screen — if the two differ, reject the transaction.
Physical Access Attacks
An attacker with physical access to your device and specialised equipment (voltage glitching, side-channel analysis) may attempt to extract the private key. These attacks are expensive ($10,000+ in equipment), time-intensive, and require expert knowledge. They are a realistic threat only for very high-value targets.
Defence: Secure element chips (Ledger, Keystone) are specifically designed to resist physical extraction. Trezor without a secure element is theoretically more vulnerable to physical attacks — offset this by using a strong passphrase (which is not stored on the device). Keep your device in a secure location and set a strong PIN that locks after failed attempts.
The $5 Wrench Attack
The most low-tech attack: someone threatens you with physical violence to hand over your crypto. No hardware security feature protects against coercion.
Defence: Use a passphrase to create a hidden wallet. Your base wallet (visible without the passphrase) holds a small decoy amount. Under duress, you hand over the device and the base PIN — the attacker sees a wallet with a plausible small balance and cannot detect the hidden passphrase-protected wallet containing your real holdings. This only works if you have set it up in advance.
Clipboard Hijacking
Malware on your computer monitors your clipboard and replaces cryptocurrency addresses when you copy-paste them. You copy your intended recipient address, but the malware substitutes an attacker's address before you paste it into the transaction form. This attack works even with hardware wallets if you do not verify the address on the device screen.
Defence: Always verify the full recipient address on your hardware wallet's screen — character by character — before confirming any transaction. The device screen cannot be manipulated by malware on your computer. If the address on the device screen does not match what you intended, reject the transaction immediately. For frequently used addresses, use your hardware wallet's address book feature (available on Ledger and Trezor) to avoid manual address entry entirely.
Fake Firmware Updates
An attacker creates a convincing email or website claiming your hardware wallet needs an urgent firmware update to fix a critical vulnerability. The link leads to a fake update tool that either installs malicious firmware or asks for your seed phrase as part of the "update process." Ledger users were targeted with this exact attack after the 2020 customer data breach.
Defence: Only update firmware through official companion apps: Ledger Live, Trezor Suite, or the Keystone update tool. Never follow firmware update links from emails, social media, or search engine ads. If you receive a notification about a critical update, navigate directly to the manufacturer's official website by typing the URL manually — do not click any links.
Hardware Wallets and DeFi
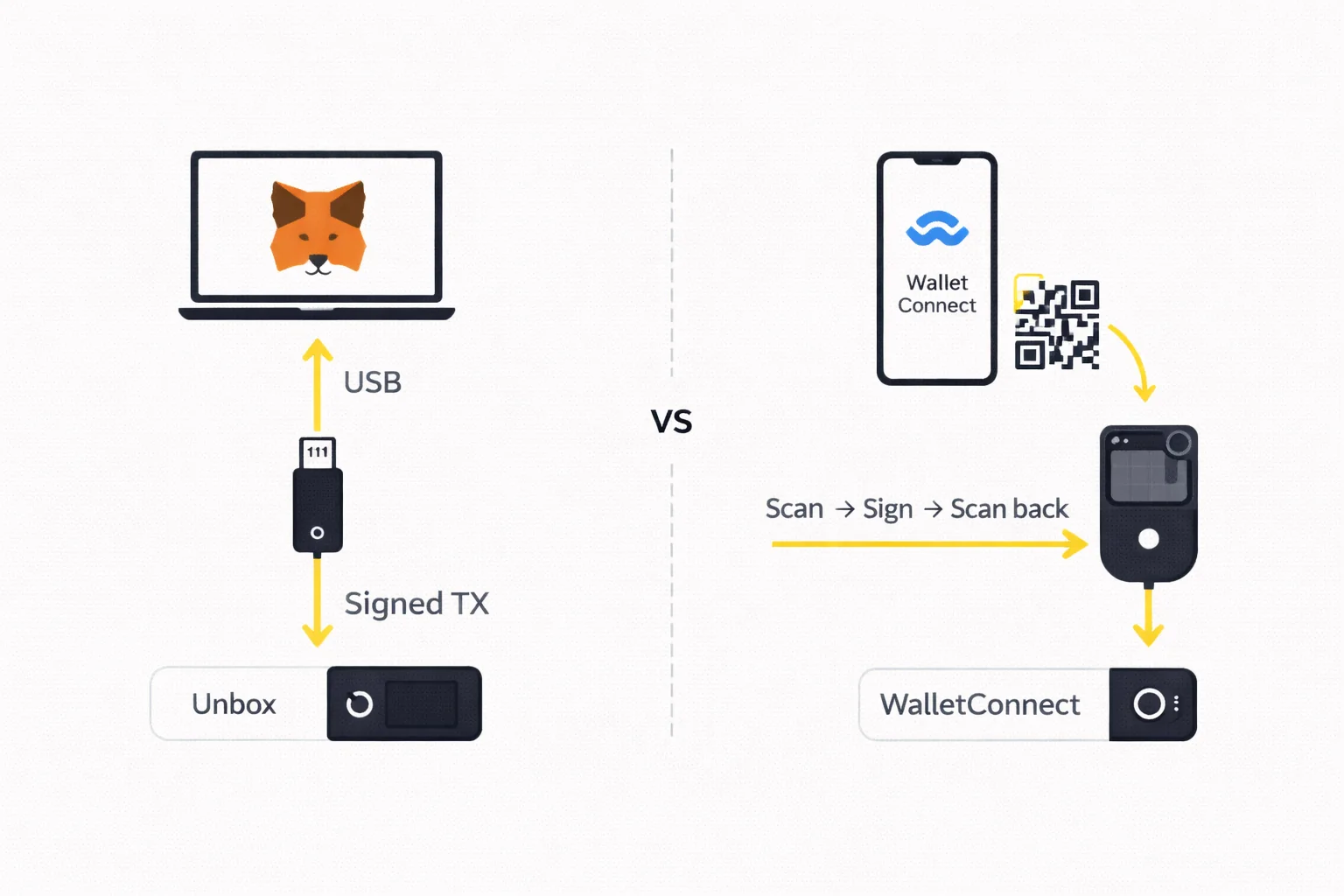
MetaMask Integration
The most common way to use a hardware wallet with DeFi is through MetaMask. Both Ledger and Trezor integrate directly: you connect your device, and MetaMask uses it as a signing backend. When you interact with a DApp (swap on Uniswap, supply on Aave, provide liquidity on Curve), MetaMask sends the unsigned transaction to your hardware wallet for verification and signing. Your keys never enter MetaMask or your browser — they stay on the device.
To set this up: open MetaMask → Settings → Connect Hardware Wallet → select your device → choose which accounts to import. From that point, every transaction requires physical confirmation on the hardware wallet. This adds 5–10 seconds per transaction but ensures that even a fully compromised browser cannot move your funds without your physical approval.
WalletConnect for Air-Gapped Devices
Keystone cannot connect directly to MetaMask via USB (it has no data port). Instead, it uses the WalletConnect protocol: scan a QR code to pair with MetaMask Mobile or a desktop DApp, then sign each transaction via the QR scan-sign-scan cycle. This works with 100+ DeFi protocols but adds friction — each transaction takes 30–45 seconds instead of 5–10 seconds with a USB-connected Ledger.
Tangem also works via WalletConnect through its companion app. You pair with a DApp, review the transaction on your phone, and tap the Tangem card to sign. The NFC signing is faster than Keystone's QR flow (2–3 seconds per tap) but you must trust your phone screen for transaction verification since the card has no display.
Blind Signing Risks
Some DeFi transactions display as raw data on your hardware wallet screen — a hexadecimal string rather than human-readable details like "Swap 1 ETH for 2,500 USDC on Uniswap." This is called blind signing, and it is dangerous: you cannot verify what you are actually approving. A malicious DApp could present a friendly interface on your computer while the actual transaction drains your wallet.
To reduce blind signing risk: use DApps that support EIP-712 typed data signing (which displays structured, readable transaction details on your device screen). Ledger has been expanding "clear signing" support for major DeFi protocols including Uniswap, Aave, and Lido. Before signing any transaction, verify that the contract address, token amounts, and recipient address on your device screen match what you expect. If the device shows unreadable data for a high-value transaction, consider using a transaction simulation tool like Tenderly or Blocknative to preview the outcome before signing.
Practical DeFi Workflow with Hardware Wallets
The most efficient setup for active DeFi users combines a hardware wallet with MetaMask. Keep your hardware wallet connected (Ledger via USB) or paired (Keystone via WalletConnect) while working through a DeFi session. Batch your transactions — approve tokens, supply collateral, and adjust positions in a single session rather than connecting and disconnecting repeatedly.
For Keystone users, the QR workflow means each DeFi interaction takes 30–45 seconds rather than 5–10 seconds. If you sign 20+ transactions daily, this friction compounds to 10–15 minutes of additional QR scanning. Consider using Keystone for high-value, infrequent transactions (large deposits, withdrawals, collateral adjustments) and a separate hot wallet with a small balance for frequent low-value interactions like governance votes or small swaps.
Regardless of which hardware wallet you use for DeFi, revoke unnecessary token approvals regularly. When you approve a DApp to spend your tokens, that approval persists until you manually revoke it. A compromised DApp could drain approved tokens months after your last interaction. Use revoke.cash or Etherscan's token approval checker monthly to audit and revoke stale approvals.
Decision Matrix
If you hold Bitcoin and want full transparency: Choose Trezor. Open-source firmware, Sparrow/Electrum integration for coin control, and a proven 12-year track record. The Model One at $69 is the most affordable genuine cold storage option available.
If you use DeFi across multiple chains: Choose Ledger. The widest app ecosystem (5,500+ tokens), MetaMask integration via USB, and Bluetooth for mobile signing. Ledger Live provides a unified interface for managing assets across Ethereum, Polygon, Arbitrum, Solana, and dozens of other networks.
If security is your absolute priority: Choose Keystone. Air-gap isolation means your device never connects to anything. Open-source firmware and an EAL5+ secure element provide the strongest combination of transparency and hardware protection. Accept the QR workflow friction as the cost of maximum security.
If you want the simplest possible experience: Choose Tangem. No seed phrase to manage, 3-minute setup, NFC tap to sign. Ideal for users who find traditional hardware wallets intimidating, or as a gift for someone entering crypto for the first time. The 3-card set ($55–70) provides built-in backup without any seed phrase management.
What If You Cannot Decide?
If you are still uncertain after reading this guide, start with the Trezor Model One at $69. It provides genuine cold storage with open-source firmware at the lowest price point in the market. You can always upgrade to a Ledger, Keystone, or Tangem later as your needs evolve and your portfolio grows — your crypto stays on the blockchain regardless of which specific hardware device holds the signing keys. What matters most is getting your holdings off centralised exchanges and into genuine self-custody as soon as possible, not finding the theoretically perfect device.
For users with larger portfolios ($50,000+), consider owning two different devices from different manufacturers. Use one as your primary signing device and store the other (with the same seed phrase restored) in a secure off-site location as a backup. This protects against the unlikely scenario of a manufacturer-specific vulnerability or supply chain issue affecting a single brand. A Ledger primary with a Trezor backup (or vice versa) provides both hardware diversity and independent seed phrase verification.
If you manage crypto for a business or trust, engage a security consultant who specialises in cryptocurrency custody to design your setup. Multisig configurations, key ceremony procedures, and inheritance planning require careful design that goes beyond individual user needs. The hardware wallets covered in this guide all support institutional workflows, but the operational procedures around them — including key ceremony documentation, access control policies, succession planning, and regular security audits — are equally important and should be professionally reviewed before deploying in a business context.
Conclusion
Hardware wallets are the most effective security measure available to individual crypto holders. By isolating your private keys from internet-connected devices, they eliminate the remote theft vector that accounts for the vast majority of crypto losses. The four major architectures — Ledger's secure element, Trezor's open-source approach, Keystone's air-gap, and Tangem's seedless NFC — each solve the same fundamental problem with different tradeoffs.
For most users, the decision comes down to three factors: how much you hold (which determines whether you need basic cold storage or premium multi-layered security), how often you transact (which determines your tolerance for signing friction and QR code workflows), and how technically comfortable you are (which determines whether open-source auditability or a guided app-based setup matters more to your daily experience).
Regardless of which device you choose, three practices are non-negotiable. First, buy only from official manufacturer websites — not Amazon, eBay, or third-party resellers where supply chain attacks are documented. Second, secure your seed phrase in at least two physically separate offline locations, ideally on a metal backup plate that survives fire and water damage. Third, verify every transaction on the hardware wallet's own screen before signing — not on your computer screen, which can be manipulated by malware. These habits protect you against the three most common attack vectors and cost nothing beyond a few seconds of attention per transaction.
The hardware wallet market in 2026 offers genuine choice for the first time. Five years ago, Ledger and Trezor were the only serious options. Today, Keystone's air-gap architecture and Tangem's seedless card design represent fundamentally new approaches to the same problem. Healthy competition has driven retail prices down (Tangem's 3-card set at $55 would have been unthinkable in 2020) while pushing security standards up (EAL5+ certification, open-source firmware, and reproducible builds are now table stakes rather than premium features).
If you take one action from this guide, let it be this: move any crypto holdings above $1,000 off exchanges and into a hardware wallet within the next week. The specific device matters less than the act of taking custody. Exchange hacks, freezes, and bankruptcies (FTX, Celsius, Voyager) have demonstrated repeatedly that "not your keys, not your coins" is not a slogan — it is a statement of legal and practical reality. When FTX collapsed in November 2022, users who had withdrawn to hardware wallets lost nothing. Users who trusted the exchange lost billions.
The total cost of a hardware wallet setup — device ($55–170 for most users), metal seed phrase backup ($30), and 15–30 minutes of setup time — is trivial compared to what you are protecting. If you hold $5,000 in crypto, you are spending 1–3% on security infrastructure that eliminates the most common loss vectors. If you hold $50,000, the cost is 0.1–0.3%. There is no other single investment with a comparable risk-reduction-to-cost ratio anywhere in the cryptocurrency security space today.
For detailed hands-on assessments of each device, see our individual reviews: Ledger, Trezor, Keystone, and Tangem. For side-by-side comparisons, see Trezor vs Ledger and Ledger vs Tangem.
Sources and References
- Ledger Academy — official security documentation
- Trezor Learn — open-source wallet education
- Keystone Security — air-gap security model documentation
- Bitcoin.org Wallet Chooser — independent wallet selection guide
- Ethereum.org Wallet Guide — Ethereum Foundation wallet security documentation
Frequently Asked Questions
- What is the safest type of hardware wallet?
- Air-gapped wallets like Keystone offer the strongest isolation since they never connect to any network. Secure element wallets like Ledger provide EAL5+ certified key protection. The safest choice depends on your threat model: air-gap for maximum isolation, secure element for convenience with strong protection.
- Do I need a hardware wallet if I have less than $1,000 in crypto?
- For holdings under $1,000, a reputable exchange with 2FA enabled is adequate. Hardware wallets become worthwhile above $1,000–5,000 where the cost of the device ($60–280) is a small fraction of what you are protecting.
- Can hardware wallets be hacked?
- No major hardware wallet has been remotely hacked. Physical attacks exist but require direct device access and specialised equipment. The main risks are phishing (tricking you into entering your seed phrase on a fake site) and supply chain attacks (buying a tampered device from an unofficial seller).
- What happens if I lose my hardware wallet?
- Your funds are safe as long as you have your recovery seed phrase. You can restore your wallet on a new device of the same brand or any compatible wallet. The hardware device stores the keys that control access to your crypto on the blockchain — not the crypto itself.
- Ledger vs Trezor vs Keystone — which should I choose?
- Ledger for the widest app ecosystem and Bluetooth mobile support. Trezor for open-source firmware transparency. Keystone for maximum air-gap security via QR codes. Tangem for a seedless NFC card design that eliminates seed phrase management entirely.
- How long does it take to set up a hardware wallet?
- Setup times vary by device: Tangem takes 3 minutes, Ledger takes 8 minutes, Trezor takes 10 minutes, and Keystone takes 25 minutes. The additional time for Keystone comes from learning the QR code workflow. All devices require writing down a seed phrase (except Tangem) and enabling security features.
- Can I use a hardware wallet with DeFi protocols?
- Yes. Ledger and Trezor connect to MetaMask via USB for direct DeFi access on Ethereum, Polygon, Arbitrum, and other EVM chains. Keystone works through WalletConnect and QR codes. Tangem connects via its companion app and WalletConnect. All four support DeFi signing with varying levels of convenience.
- What is a seed phrase and why is it important?
- A seed phrase is a sequence of 12 or 24 English words generated during hardware wallet setup. It is the master backup for all your cryptocurrency keys. If your device is lost or damaged, the seed phrase restores full access on a new device. Losing your seed phrase means permanent loss of funds — secure it in multiple offline locations.
- Should I buy a used hardware wallet?
- No. A used device could be pre-configured with a known seed phrase, allowing the previous owner to drain funds you deposit. Always buy new from the official manufacturer website or authorised retailers. Verify tamper-evident packaging is intact before setup.
- How do Tangem backup cards work?
- During initial setup, Tangem clones your private key onto 2–3 additional NFC cards. Each card is an identical backup — tap any card to sign transactions. If you lose one card, the others maintain full access. Unlike seed phrases, you cannot write down a Tangem backup — the key exists only inside the physical cards.
← Back to Crypto Investing Blog Index
Financial Disclaimer
This content is not financial advice. All information provided is for educational purposes only. Cryptocurrency investments carry significant investment risk, and past performance does not guarantee future results. Always do your own research and consult a qualified financial advisor before making investment decisions.
Affiliate Disclosure
This page contains affiliate links. When you sign up through our referral links, we may earn a commission at no additional cost to you. This helps support our platform and allows us to continue providing valuable content and recommendations.