Cloud Hosting Guide: Best Providers
Introduction
Cloud hosting transforms crypto projects. The right provider determines success. Industry growth demands better solutions. Your choice matters significantly. Technology evolves rapidly today.
Cloud system has revolutionised how cryptocurrency and blockchain projects deploy, scale, and maintain their digital services in 2025. As the cryptocurrency industry matures, the demand for reliable, secure, and scalable hosting solutions has never been greater. Choosing the right cloud provider can determine your project's success or failure.
Crypto platforms face unique challenges. Trading requires instant execution. Nodes consume massive bandwidth. Security protects user funds. Reliability ensures continuous operation.
The cryptocurrency space presents unique hosting challenges that traditional web applications rarely encounter. High-frequency trading platforms require ultra-low latency, whilst blockchain nodes demand substantial storage and bandwidth resources. DeFi systems need bulletproof security to protect millions of dollars, and these requirements have pushed cloud providers to develop specialised services tailored for cryptocurrency applications.
Cloud hosting evolves constantly. Options improve every year. Competition drives innovation forwards. Providers compete for customers. Markets reward better service.
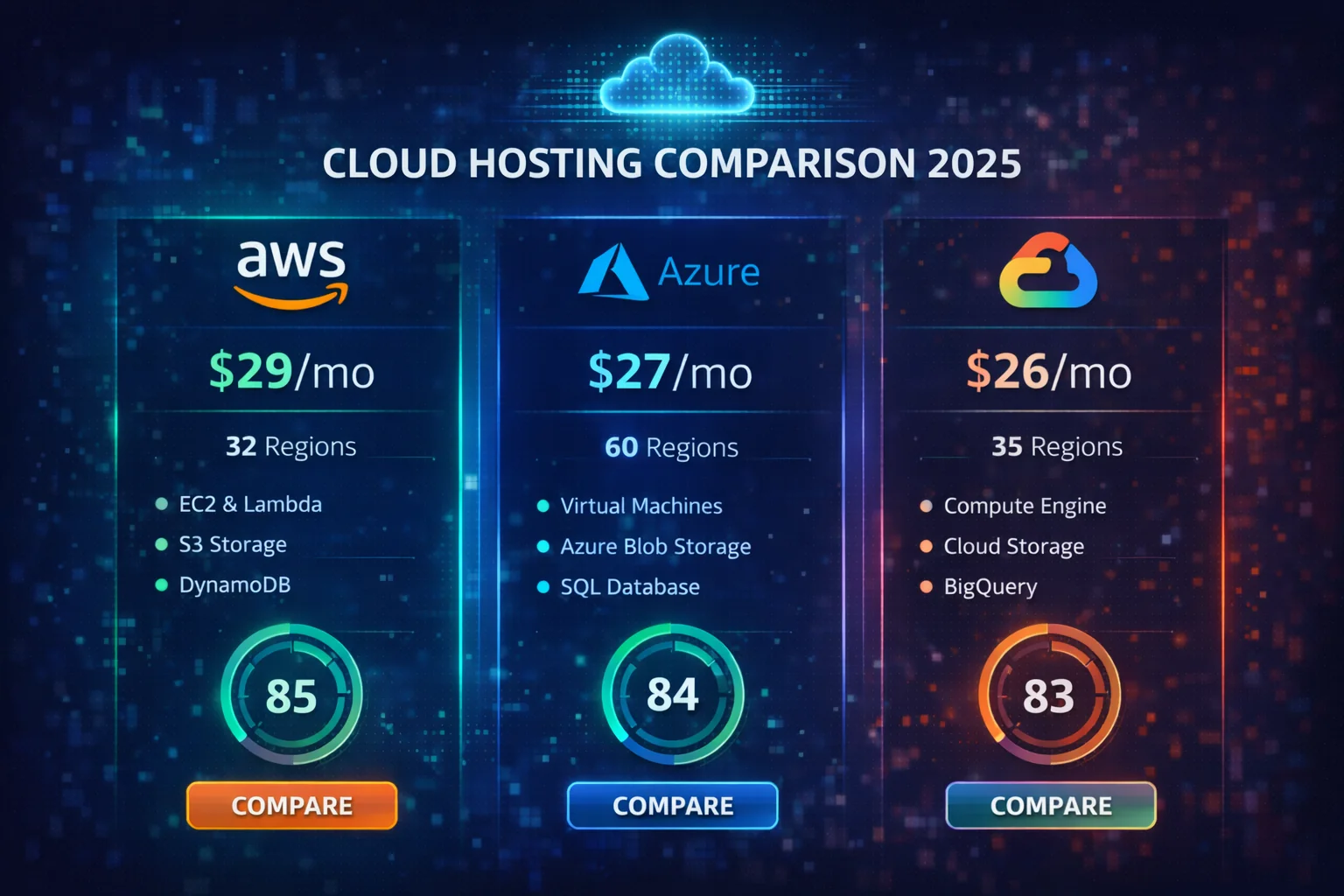
In 2025, the cloud hosting landscape offers unprecedented opportunities as major providers like AWS, Google Cloud, and Microsoft Azure have introduced blockchain-specific services. Developer-friendly platforms like DigitalOcean provide cost-effective solutions for smaller projects, whilst emerging technologies like edge computing, serverless architectures, and container orchestration create new possibilities for scalable cryptocurrency infrastructure.
Security protects your assets. Breaches destroy trust permanently. Modern providers offer protection.
Security remains the paramount concern for any cryptocurrency project, as crypto platforms handle irreversible financial transactions and store valuable digital assets. A single security breach can result in permanent loss of funds and irreparable damage to reputation, which is why modern cloud providers have responded with enterprise-grade security features specifically designed for cryptocurrency applications.
Regulations shape hosting decisions. Countries enforce different rules. Compliance protects your business. Legal requirements vary globally. Jurisdictions differ significantly worldwide.
The regulatory landscape also influences hosting decisions, as different jurisdictions have varying requirements covering data residency, user privacy, and financial services compliance. Cloud providers with global infrastructure enable projects to deploy resources in specific regions, meeting regulatory requirements whilst maintaining optimal performance for users worldwide.
This guide helps you choose. We compare major providers. Features and pricing matter. Security determines long-term success. Infrastructure quality affects performance. Reliability builds user trust.
This guide examines the top cloud hosting providers for cryptocurrency projects in 2025, comparing their features, pricing, security capabilities, and suitability for different use cases. We explore everything from basic website hosting to enterprise-grade infrastructure, providing the insights you need to make informed decisions.
Performance determines user experience. Speed attracts more customers. Latency drives users away. Milliseconds matter in trading.
Performance optimisation becomes critical as cryptocurrency applications require real-time data processing, high-frequency trading capabilities, and instant transaction confirmations. Modern cloud providers offer specialised services including dedicated instances, GPU computing, and ultra-low latency networking to meet these demanding requirements.
Costs require careful planning. Budgets need accurate forecasting. Pricing affects long-term viability. Hidden fees add up.
Cost considerations extend beyond simple server rental fees to include bandwidth usage for blockchain synchronization, storage requirements for transaction history, and computational resources for smart contract execution. Understanding these cost structures is essential for building sustainable cryptocurrency businesses that can scale efficiently.
The competitive landscape amongst cloud providers has intensified significantly. This competition benefits cryptocurrency projects through improved pricing, enhanced features, and specialised blockchain services. Major providers now offer managed blockchain services, dedicated cryptocurrency node hosting, and optimised configurations for DeFi applications. Smaller providers compete by offering superior customer support, simplified pricing models, and developer-friendly interfaces.
Providers compete for customers. Features improve constantly. Prices become more competitive. Innovation accelerates development speed.
Downtime destroys crypto businesses. Backups prevent total losses. Planning saves your project. Recovery systems work automatically.
Disaster recovery and business continuity planning represent critical considerations for cryptocurrency projects. Unlike traditional applications where downtime causes inconvenience, cryptocurrency service interruptions can result in missed trading opportunities, failed transactions, and significant financial losses. Modern cloud providers offer sophisticated backup solutions, multi-region redundancy, and automated failover capabilities that ensure continuous operation even during major infrastructure failures.
Sustainability attracts conscious investors. Green hosting builds reputation. Eco-friendly choices matter now. Carbon neutrality gains importance.
Environmental sustainability has become an increasingly important consideration for cryptocurrency projects selecting cloud infrastructure. Major cloud providers have committed to carbon neutrality and renewable energy initiatives, enabling cryptocurrency projects to reduce their environmental footprint whilst maintaining high-performance infrastructure. This alignment with sustainability goals has become particularly relevant as proof-of-stake networks and energy-efficient blockchain technologies gain prominence in the industry.
What is Cloud Services?
Cloud services use multiple interconnected servers to host websites and applications, providing better reliability, scalability, and performance than traditional single-server hosting. Resources are distributed across a network of servers, ensuring your project stays online even if individual servers fail.
Key Benefits of Cloud Infrastructure
Cloud platforms offer several advantages over traditional server solutions:
- Scalability: Easily adjust resources based on demand
- Reliability: Multiple servers provide redundancy
- Performance: Global content delivery networks (CDNs)
- Cost-effectiveness: Pay only for resources used
- Security: Enterprise-grade security features
- Flexibility: Wide range of services and configurations
Top Cloud Infrastructure Providers
Amazon Web Services (AWS)
Amazon Web Services remains the market leader in cloud system, offering the most complete suite of services and global system. AWS is particularly well-suited for enterprise applications and complex cryptocurrency projects that require advanced features.

AWS strengths:
- Largest global system with 99+ availability zones
- Most complete service portfolio (200+ services)
- Advanced security and compliance certifications
- Excellent for blockchain and cryptocurrency applications
- Robust API system and developer tools
- Strong enterprise support and documentation
Best for: Enterprise projects, complex applications, blockchain system, high-traffic websites
DigitalOcean
DigitalOcean focuses on simplicity and developer experience, making it an excellent choice for startups, small to medium projects, and developers who want straightforward cloud solutions without complexity.
DigitalOcean advantages:
- Simple, predictable pricing structure
- Excellent developer experience and documentation
- Fast SSD-based virtual machines (Droplets)
- Strong community and tutorial resources
- Good performance for crypto websites and applications
- Managed databases and Kubernetes services
Best for: Startups, crypto websites, development projects, small to medium applications
Google Cloud Platform (GCP)
Google Cloud Platform excels in data analytics, machine learning, and modern application development. It's particularly strong for projects requiring advanced AI/ML capabilities or big data processing.
GCP highlights:
- Superior data analytics and machine learning tools
- Excellent Kubernetes and container support
- Strong performance and global network
- Competitive pricing with sustained use discounts
- Good for blockchain analytics and data processing
- Advanced security and identity management
Best for: Data-heavy applications, machine learning projects, modern web applications, analytics platforms
Microsoft Azure
Microsoft Azure is ideal for organisations already using Microsoft technologies and enterprises requiring hybrid cloud solutions. It offers strong integration with existing Microsoft system.
Azure benefits:
- Excellent integration with Microsoft system
- Strong hybrid cloud capabilities
- Comprehensive enterprise services
- Good blockchain development tools
- Competitive pricing for Windows-based workloads
- Strong compliance and security features
Best for: Enterprise applications, Microsoft-centric environments, hybrid cloud deployments
Choosing the Right Provider for Crypto Projects
Security Considerations
Security is paramount for cryptocurrency and blockchain projects. Consider these security features when choosing a cloud provider:
- DDoS protection and mitigation
- Web Application Firewall (WAF) capabilities
- SSL/TLS certificate management
- Identity and access management (IAM)
- Encryption at rest and in transit
- Compliance certifications (SOC 2, ISO 27001)
- Network security and VPC isolation
- Regular security audits and monitoring
Performance Requirements
Crypto projects often have specific performance needs that should influence your hosting choice:
- Low latency for trading applications
- High availability for critical services
- Scalability for traffic spikes
- Global content delivery for international users
- Database performance for transaction processing
- API response times for integrations
Cost Analysis and optimisation
Pricing Models Comparison
Different cloud providers use various pricing models that can greatly impact your costs:
AWS Pricing:
- Pay-as-you-go with complex pricing tiers
- Reserved instances for long-term savings
- Spot instances for cost-effective batch processing
- Free tier for new users (12 months)
DigitalOcean Pricing:
- Simple, predictable monthly pricing
- No hidden fees or complex calculations
- Transparent bandwidth and storage costs
- Good value for small to medium projects
Google Cloud Pricing:
- Per-minute billing for compute resources
- Sustained use discounts for consistent workloads
- Committed use contracts for additional savings
- Generous free tier and credits for new users
Cost optimisation Strategies
Implement these strategies to optimise your cloud system costs:
- Right-size your instances based on actual usage
- Use auto-scaling to match resources with demand
- Implement caching to reduce server load
- optimise images and static assets
- Use CDNs to reduce bandwidth costs
- Monitor and analyse usage patterns regularly
- Consider reserved instances for predictable workloads
- Implement proper resource tagging and cost allocation
Setting Up Your First Cloud Server
Initial Setup Steps
Follow these general steps when setting up your first cloud server:
- Create an account with your chosen provider
- Select the appropriate server size and location
- Choose your operating system (Ubuntu, CentOS, etc.)
- Configure SSH keys for secure access
- Set up basic security measures (firewall, updates)
- Install necessary software and dependencies
- Configure backups and monitoring
- Test your setup thoroughly
Essential Security Hardening
Secure your cloud server with these essential steps:
- Disable root login and use sudo users
- Configure SSH key authentication
- Set up a firewall (UFW, iptables)
- Enable automatic security updates
- Install and configure fail2ban
- Use strong passwords and two-factor authentication
- Regular security audits and monitoring
- Keep software and dependencies updated
specialised Hosting for Crypto Projects
Blockchain Node Hosting
Running blockchain nodes needs specific considerations for hardware and network requirements. For complete development setup, see our developer tools guide.
- High-performance SSD storage for blockchain data
- Sufficient RAM for node synchronization
- Reliable network connectivity with high bandwidth
- 24/7 uptime for network participation
- Regular backups of node data
- Monitoring for node health and synchronization
Trading Bot Infrastructure
Cryptocurrency trading bots have unique hosting requirements:
- Low latency connections to exchanges
- High availability and redundancy
- Secure API key management
- Real-time monitoring and alerting
- Automated failover methods
- Compliance with exchange requirements
Monitoring and Maintenance
Essential Monitoring Tools
Implement complete monitoring to ensure optimal performance:
- Server resource monitoring (CPU, RAM, disk)
- Application performance monitoring (APM)
- Uptime monitoring and alerting
- Security monitoring and intrusion detection
- Log aggregation and analysis
- Database performance monitoring
- Network monitoring and traffic analysis
Backup and Disaster Recovery
Protect your crypto project with robust backup and recovery procedures:
- Automated daily backups of critical data
- Off-site backup storage for disaster recovery
- Regular backup testing and restoration procedures
- Database replication for high availability
- Documentation of recovery procedures
- Regular disaster recovery testing
Scaling Your Infrastructure
Horizontal vs Vertical Scaling
Understand the different scaling approaches for growing your crypto project:
Vertical Scaling (Scale Up):
- Add more power to existing servers
- Increase CPU, RAM, or storage capacity
- Simpler to use but has limits
- Good for applications with single points of processing
Horizontal Scaling (Scale Out):
- Add more servers to distribute load
- Better fault tolerance and unlimited scaling potential
- Requires application architecture changes
- Ideal for web applications and distributed systems
Auto-Scaling Implementation
Implement auto-scaling to handle traffic fluctuations automatically:
- Define scaling triggers based on metrics
- Set minimum and maximum instance limits
- Configure health checks and replacement policies
- Test scaling policies under various load conditions
- Monitor costs and optimise scaling parameters
Compliance and Legal Considerations
Data Protection Regulations
Ensure your hosting setup complies with relevant data protection laws:
- GDPR compliance for European users
- CCPA compliance for California residents
- Data residency requirements
- User consent and data processing documentation
- Right to deletion and data portability
- Privacy policy and terms of service updates
Cryptocurrency Regulations
Consider regulatory requirements specific to cryptocurrency projects:
- KYC/AML compliance for financial services
- Licensing requirements in operating jurisdictions
- Data retention and reporting obligations
- Cross-border data transfer restrictions
- Audit trails and transaction monitoring
Future Trends in Cloud Infrastructure
Emerging Technologies
Stay ahead of the curve with these emerging cloud services trends:
- Edge computing for reduced latency
- Serverless architectures and functions
- Container orchestration with Kubernetes
- AI/ML integration for automated operations
- Quantum computing services
- Blockchain-as-a-Service (BaaS) platforms
Sustainability and Green Hosting
Environmental considerations are becoming increasingly important:
- Renewable energy-powered data centers
- Carbon-neutral hosting options
- Energy-efficient server technologies
- optimisation for reduced power consumption
- Sustainability reporting and certifications
Decision Framework
Evaluation Criteria
Use this checklist to evaluate cloud providers:
- Performance requirements and SLA guarantees
- Security features and compliance certifications
- Pricing structure and cost predictability
- Geographic coverage and data centre locations
- Support quality and response times
- Integration capabilities and API quality
- Scalability options and limitations
- Backup and disaster recovery features
Getting Started Recommendations
Based on different project types, here are our recommendations:
For Beginners: Start with DigitalOcean for its simplicity and excellent documentation
For Enterprises: Choose AWS for complete features and global system
For Data Projects: Consider Google Cloud for superior analytics and ML tools
For Microsoft Shops: Azure gives the best integration with existing Microsoft system
Cloud Infrastructure Setup Walkthrough
Step-by-Step Server Deployment
Here's a detailed walkthrough for setting up your first cloud server for a crypto project:
Phase 1: Account Setup and Planning (Day 1)
- Create provider account: Sign up with your chosen cloud provider
- Verify identity: Complete any required verification processes
- Set up billing: Add payment method and configure billing alerts
- Plan your architecture: Document server requirements and network topology
- Choose server location: Select data centre closest to your target users
Phase 2: Server Configuration (Day 1-2)
- Select server specifications: Choose CPU, RAM, and storage based on requirements
- Choose operating system: Ubuntu 22.04 LTS recommended for most crypto projects
- Configure SSH access: Generate SSH key pairs for secure access
- Set up networking: Configure VPC, subnets, and security groups
- Launch server instance: Deploy your configured server
Phase 3: Security Hardening (Day 2-3)
- Update system packages: Run full system updates
- Configure firewall: Set up UFW or iptables rules
- Install fail2ban: Protect against brute force attacks
- Set up SSL certificates: Configure Let's Encrypt or commercial SSL
- Enable monitoring: Install monitoring agents and configure alerts
Phase 4: Application Deployment (Day 3-5)
- Install runtime environment: Node.js, Python, or your preferred stack
- Set up database: Install and configure PostgreSQL, MongoDB, or MySQL
- Deploy application code: Upload and configure your crypto application
- Configure reverse proxy: Set up Nginx or Apache for web serving
- Test functionality: Verify all components work correctly
Common Setup Pitfalls to Avoid
- Skipping security hardening: Always secure your server before deploying applications
- Using default passwords: Change all default credentials immediately
- Ignoring backup setup: Configure automated backups from day one
- Overlooking monitoring: Set up monitoring and alerting before issues occur
- Poor resource planning: Start with adequate resources to avoid performance issues
Performance optimisation Techniques
Server-Level Optimizations
optimise your cloud server performance with these proven techniques:
CPU and Memory optimisation
- Right-size your instances: Monitor CPU and memory usage to choose optimal instance types
- Enable CPU credits: Use burstable instances for variable workloads
- optimise memory allocation: Configure swap space and memory limits appropriately
- Use CPU affinity: Pin critical processes to specific CPU cores
Storage Performance Tuning
- Choose appropriate storage types: SSD for databases, HDD for backups
- optimise file systems: Use ext4 or XFS for better performance
- Configure RAID: Implement RAID 10 for high-performance databases
- Enable compression: Use filesystem compression for log files
Network Performance Enhancement
Bandwidth optimisation
- Use CDN services: Distribute static content globally
- Enable compression: Gzip compression for web content
- optimise images: Use WebP format and appropriate compression
- Implement caching: Redis or Memcached for application caching
Latency Reduction
- Choose optimal regions: Deploy close to your users
- Use connection pooling: Reduce database connection overhead
- Enable HTTP/2: Improve web application performance
- optimise DNS: Use fast DNS providers like Cloudflare
Database Performance Tuning
PostgreSQL optimisation for Crypto Applications
- Configure shared_buffers: Set to 25% of available RAM
- optimise work_mem: Adjust based on concurrent connections
- Enable query optimisation: Use EXPLAIN analyse for slow queries
- Implement proper indexing: Index frequently queried columns
- Configure connection pooling: Use PgBouncer for connection management
MongoDB optimisation for Blockchain Data
- Use appropriate storage engines: WiredTiger for most use cases
- optimise index strategies: Compound indexes for complex queries
- Configure sharding: Distribute data across multiple servers
- Enable compression: Reduce storage requirements
- Monitor performance metrics: Use MongoDB Compass or similar tools
Security Best Practices (Detailed)
Network Security Implementation
Firewall Configuration
Implement complete firewall rules for crypto applications:
- Default deny policy: Block all traffic by default, allow only necessary ports
- SSH access control: Limit SSH to specific IP addresses or VPN
- Application ports: Open only required ports (80, 443, custom API ports)
- Database security: Never expose database ports to the internet
- Regular rule audits: Review and update firewall rules monthly
VPN and Private Networks
- Set up VPC: Use Virtual Private Cloud for network isolation
- Implement VPN access: WireGuard or OpenVPN for secure remote access
- Use private subnets: Keep databases and internal services private
- Network segmentation: Separate production, staging, and development environments
Application Security Measures
API Security for Crypto Applications
- Implement rate limiting: Prevent API abuse and DDoS attacks
- Use API authentication: JWT tokens or API keys with proper rotation
- Enable CORS properly: Configure Cross-Origin Resource Sharing securely
- Input validation: Validate and sanitize all user inputs
- Implement HTTPS everywhere: Force SSL/TLS for all communications
Data Protection Strategies
- Encrypt sensitive data: Use AES-256 for data at rest
- Secure key management: Use cloud provider key management services
- Implement data masking: Mask sensitive data in logs and development environments
- Regular security audits: Conduct quarterly security assessments
- Compliance monitoring: Ensure ongoing compliance with relevant regulations
Incident Response Planning
Security Incident Procedures
- Immediate containment: Isolate affected systems
- Damage assessment: Evaluate scope and impact
- Evidence preservation: Maintain logs and forensic data
- Stakeholder notification: Inform relevant parties and authorities
- Recovery useation: Restore services from clean backups
- Post-incident review: analyse and improve security measures
Business Continuity Planning
- Disaster recovery sites: Maintain backup system in different regions
- Data replication: Real-time or near-real-time data synchronization
- Automated failover: Implement automatic switching to backup systems
- Regular testing: Test disaster recovery procedures quarterly
- Documentation maintenance: Keep recovery procedures updated
Enterprise Cloud Strategies and Advanced Infrastructure Management
Multi-Cloud Architecture and Hybrid Infrastructure Solutions
Enterprise cryptocurrency and blockchain projects increasingly use advanced multi-cloud strategies that leverage the unique strengths of different cloud providers. maintaining operational resilience, cost optimisation, and regulatory compliance across multiple jurisdictions. These advanced architectures include hybrid cloud deployments that combine on-premises system with multiple public cloud providers, edge computing useations that optimise performance for global user bases, and complete disaster recovery strategies that ensure business continuity under various failure scenarios.
Professional multi-cloud useations require advanced orchestration platforms that manage workloads across different providers, automated failover systems that ensure high availability, and complete monitoring solutions that provide unified visibility across complex distributed systems. Advanced users use container orchestration platforms like Kubernetes that enable portable workloads, service mesh architectures that optimise inter-service communication, and complete security structures that maintain consistent protection across multiple cloud environments.
Hybrid system strategies enable organisations to optimise costs by leveraging different pricing models, maintain data sovereignty by keeping sensitive information in specific jurisdictions, and use advanced compliance structures that meet regulatory requirements across multiple regions. Professional useations include automated workload placement based on cost and performance criteria, dynamic scaling strategies that optimise resource utilisation, and complete governance structures that ensure consistent policies across all system components.
Advanced Security and Compliance Frameworks
Enterprise cloud security for cryptocurrency and blockchain applications needs complete structures that address both traditional cybersecurity threats and blockchain-specific vulnerabilities. maintaining operational efficiency and regulatory compliance. Advanced security useations include zero-trust network architectures, complete identity and access management systems, advanced threat detection and response capabilities, and professional-grade encryption strategies that protect sensitive data and cryptographic keys across all system components.
Compliance structures for cryptocurrency projects must address multiple regulatory requirements including data protection regulations, financial services compliance, and blockchain-specific regulatory guidance across different jurisdictions. Professional useations include automated compliance monitoring, complete audit trails, advanced data governance structures, and specialised security controls that meet the unique requirements of cryptocurrency and blockchain applications. maintaining operational efficiency and user experience.
Advanced security strategies include hardware security modules for cryptographic key management, complete vulnerability management programs, advanced incident response procedures, and professional-grade security monitoring that gives real-time threat detection and automated response capabilities. Enterprise users use defence-in-depth strategies, regular security assessments, complete staff training programs, and advanced backup and recovery procedures that ensure business continuity under various threat scenarios.
Performance optimisation and Cost Management
Professional cloud system management needs advanced performance optimisation strategies that balance cost efficiency with operational requirements. maintaining high availability and user experience standards. Advanced optimisation techniques include automated resource scaling based on demand patterns, intelligent workload placement that optimises performance and costs, complete performance monitoring that identifies optimisation opportunities, and advanced cost management structures that ensure optimal resource utilisation across all system components.
Cost optimisation strategies for cryptocurrency projects include reserved instance planning that reduces long-term costs, spot instance utilisation for non-critical workloads, complete resource tagging and allocation tracking, and automated cost monitoring that gives real-time visibility into system expenses. Professional users use advanced budgeting and forecasting systems, automated cost optimisation recommendations, and complete reporting capabilities that enable informed decision-making about system investments and optimisation opportunities.
Performance optimisation needs complete understanding of application requirements, user behavior patterns, and system capabilities that enable optimal resource allocation and configuration. Advanced users use content delivery networks for global performance optimisation, database optimisation strategies that improve application responsiveness, advanced caching useations that reduce system load, and complete monitoring systems that provide real-time visibility into performance metrics and optimisation opportunities across all system components.
DevOps Integration and Automation Strategies
Modern cloud system management increasingly relies on advanced DevOps practices and automation structures that enable efficient deployment, monitoring, and management of complex cryptocurrency and blockchain applications. Advanced DevOps useations include complete continuous integration and deployment pipelines, system-as-code structures that enable consistent and repeatable deployments, automated testing strategies that ensure application quality, and advanced monitoring and alerting systems that provide real-time visibility into application and system performance.
Automation strategies for cryptocurrency projects include automated security scanning and vulnerability management, advanced deployment orchestration that minimises downtime, complete backup and recovery automation, and intelligent resource management that optimises costs and performance based on real-time demand patterns. Professional users use GitOps workflows, complete configuration management, automated compliance checking, and advanced rollback procedures that ensure reliable and efficient system operations.
Integration strategies require complete understanding of development workflows, operational requirements, and business objectives that enable optimal toolchain selection and configuration. Advanced users use advanced monitoring and observability platforms, automated incident response procedures, complete documentation and knowledge management systems, and professional-grade change management processes that ensure reliable and efficient system evolution. maintaining security, compliance, and operational excellence standards.
Advanced Cloud Strategies and Enterprise Implementation
Multi-Cloud Architecture and Hybrid Deployment Strategies
Professional cryptocurrency system increasingly uses multi-cloud architectures that distribute workloads across multiple cloud providers to optimise performance, reduce vendor lock-in, and enhance resilience against provider-specific outages or service limitations. Advanced multi-cloud strategies include intelligent workload placement based on cost optimisation, performance requirements, and regulatory compliance needs. maintaining consistent security standards and operational procedures across all cloud environments.
Hybrid cloud useations combine public cloud services with private system to balance cost efficiency with security requirements, enabling cryptocurrency projects to maintain sensitive operations on-premises whilstleveraging cloud scalability for variable workloads. Professional hybrid strategies include advanced data synchronization, complete security structures that span multiple environments, and advanced networking solutions that provide seamless connectivity between cloud and on-premises system. maintaining performance and security standards.
Enterprise-grade multi-cloud orchestration needs advanced management platforms that provide unified visibility and control across diverse cloud environments. These platforms enable automated workload migration based on cost optimisation algorithms, performance monitoring that identifies optimal resource allocation strategies, and complete governance structures that ensure consistent security policies and compliance standards across all cloud providers. Advanced orchestration includes intelligent traffic routing, automated disaster recovery procedures, and advanced cost optimisation strategies that leverage the unique pricing models and capabilities of different cloud providers.
Professional hybrid cloud architectures use advanced networking solutions including dedicated private connections, software-defined networking overlays, and complete security structures that enable seamless integration between public cloud services and private system. These useations include advanced data classification and placement strategies, automated compliance monitoring across multiple environments, and complete backup and recovery procedures that ensure business continuity. maintaining optimal performance and cost efficiency across all system components.
Container Orchestration and Microservices Architecture
Modern cryptocurrency applications increasingly use containerized architectures that enable efficient resource utilisation, simplified deployment procedures, and enhanced scalability through advanced orchestration platforms like Kubernetes. Advanced container strategies include automated scaling based on demand patterns, complete service mesh useations that provide advanced networking and security capabilities, and advanced monitoring solutions that provide real-time visibility into application performance and resource utilisation across distributed container environments.
Microservices architectures enable cryptocurrency projects to build scalable, maintainable applications through modular design principles that separate concerns and enable independent scaling of different application components. Professional microservices useations include complete API management, advanced service discovery methods, advanced load balancing strategies, and complete monitoring and observability solutions that provide insights into complex distributed systems. maintaining performance and reliability standards.
Advanced Kubernetes useations for cryptocurrency applications include advanced cluster management strategies that optimise resource allocation across multiple availability zones, complete security structures that use pod security policies and network segmentation, and advanced monitoring solutions that provide detailed insights into application performance and resource utilisation. Professional Kubernetes deployments include automated certificate management, advanced ingress controllers that optimise traffic routing, and complete backup and disaster recovery procedures that ensure business continuity. maintaining optimal performance and security standards.
Service mesh architectures provide advanced networking capabilities including intelligent traffic routing, complete security policies, and advanced observability features that enable optimal performance and security for complex microservices applications. Professional service mesh useations include automated certificate rotation, complete traffic encryption, advanced rate limiting and circuit breaker patterns, and advanced monitoring capabilities that provide detailed insights into inter-service communication patterns and performance characteristics across distributed cryptocurrency applications.
Advanced Security Architecture and Compliance Frameworks
Enterprise cryptocurrency system needs complete security architectures that address multiple threat vectors. maintaining operational efficiency and regulatory compliance across diverse jurisdictions. Advanced security useations include zero-trust networking models, complete identity and access management systems, advanced threat detection and response capabilities, and advanced encryption strategies that protect data at rest, in transit, and during processing. maintaining performance and usability standards.
Compliance structures for cryptocurrency projects must address evolving regulatory requirements including data protection regulations, financial services compliance, and blockchain-specific regulatory guidance. maintaining operational flexibility and innovation capabilities. Professional compliance useations include automated compliance monitoring, complete audit trail generation, advanced data governance structures, and specialised security controls that meet regulatory requirements. enabling efficient cryptocurrency operations and business growth.
Zero-trust security architectures use complete identity verification for all network access requests, advanced device authentication and authorisation procedures, and advanced threat detection capabilities that monitor all network traffic and user behavior patterns. Professional zero-trust useations include complete endpoint protection, advanced network segmentation strategies, advanced behavioral analytics that identify potential security threats, and complete incident response procedures that enable rapid containment and remediation of security incidents. maintaining operational continuity and user experience standards.
Advanced encryption strategies for cryptocurrency system include complete key management systems that protect cryptographic keys throughout their lifecycle, advanced data classification structures that ensure appropriate protection levels for different data types, and advanced encryption algorithms that provide optimal security. maintaining performance and usability standards. Professional encryption useations include hardware security modules for critical key operations, complete key rotation procedures, advanced access controls that limit key access to authorized personnel, and complete audit trails that document all key management operations for compliance and security monitoring purposes.
Performance optimisation and Global Infrastructure
Professional cryptocurrency applications require advanced performance optimisation strategies that ensure optimal user experience across global audiences. managing system costs and complexity. Advanced performance strategies include intelligent content delivery networks that optimise asset delivery based on user location and device capabilities, advanced caching useations that reduce server load and improve response times, and complete performance monitoring that identifies optimisation opportunities and potential bottlenecks across all system components.
Global system deployment needs complete understanding of regional performance characteristics, regulatory requirements, and user behavior patterns that enable optimal data centre selection and resource allocation. Professional global strategies include intelligent traffic routing based on real-time performance metrics, advanced disaster recovery procedures that ensure business continuity across multiple regions, and complete monitoring solutions that provide visibility into global system performance and user experience metrics.
Advanced content delivery network useations for cryptocurrency applications include advanced edge computing capabilities that enable real-time data processing at network edges, complete caching strategies that optimise performance for different content types and user access patterns, and intelligent traffic routing algorithms that automatically select optimal delivery paths based on real-time network conditions and performance metrics. Professional CDN deployments include complete security features, advanced analytics capabilities, and advanced integration with cloud system that allows seamless scaling and optimisation of global content delivery performance.
Database optimisation strategies for global cryptocurrency applications include advanced replication and sharding techniques that distribute data across multiple regions. maintaining consistency and performance standards, advanced caching useations that reduce database load and improve response times, and complete monitoring solutions that provide insights into database performance and optimisation opportunities. Professional database deployments include automated backup and recovery procedures, advanced security controls that protect sensitive data, and advanced performance tuning strategies that optimise query performance and resource utilisation across distributed database environments.
Cost optimisation and Resource Management Excellence
Enterprise cloud system management needs advanced cost optimisation strategies that balance performance requirements with budget constraints. maintaining operational excellence and growth capabilities. Advanced cost optimisation includes automated resource rightsizing based on utilisation patterns, intelligent workload scheduling that leverages spot instances and reserved capacity, complete cost allocation and chargeback systems, and advanced forecasting models that enable informed system investment decisions and budget planning.
Resource management excellence encompasses complete monitoring and analytics that provide insights into resource utilisation patterns, automated optimisation recommendations that identify cost-saving opportunities, and advanced governance structures that ensure optimal resource allocation across different projects and teams. Professional resource management includes complete tagging strategies, automated cost reporting and alerting, and advanced optimisation tools that enable continuous improvement of system efficiency and cost effectiveness. maintaining performance and reliability standards.
Advanced cost optimisation strategies include advanced workload analysis that identifies opportunities for reserved instance purchases, intelligent spot instance utilisation that reduces costs for non-critical workloads, and complete cost allocation structures that enable accurate chargeback and budget management across different business units and projects. Professional cost optimisation includes automated rightsizing recommendations based on historical usage patterns, advanced forecasting models that predict future resource requirements, and complete reporting capabilities that provide detailed insights into cost trends and optimisation opportunities across all system components.
Resource governance structures for cryptocurrency projects include complete policy enforcement that ensures optimal resource allocation and utilisation, advanced approval workflows that control system provisioning and changes, and advanced monitoring capabilities that provide real-time visibility into resource usage and compliance with organisational policies. Professional governance useations include automated policy compliance checking, complete audit trails that document all resource allocation decisions, and advanced reporting capabilities that enable informed decision-making about system investments and optimisation strategies.
DevOps Excellence and Automation Frameworks
Modern cryptocurrency system management relies on advanced DevOps practices and automation structures that enable efficient development, deployment, and operations. maintaining security and compliance standards. Advanced DevOps useations include complete continuous integration and deployment pipelines, system-as-code structures that enable consistent and repeatable deployments, advanced testing strategies that ensure application quality, and complete monitoring and observability solutions that provide real-time insights into application and system performance.
Automation structures for cryptocurrency projects include intelligent deployment orchestration, automated security scanning and vulnerability management, advanced backup and recovery procedures, and complete configuration management that ensures consistent system state across all environments. Professional automation strategies include GitOps workflows, complete policy enforcement, automated compliance checking, and advanced rollback procedures that enable reliable and efficient system operations. maintaining security, performance, and operational excellence standards.
Advanced continuous integration and deployment pipelines for cryptocurrency applications include advanced testing structures that validate application functionality, security, and performance across multiple environments, automated security scanning that identifies vulnerabilities and compliance issues, and complete deployment orchestration that allows zero-downtime deployments. maintaining application availability and user experience standards. Professional CI/CD useations include advanced branching strategies, complete code review processes, automated quality gates that ensure code quality standards, and advanced monitoring capabilities that provide real-time feedback on deployment success and application performance.
Infrastructure-as-code structures enable consistent and repeatable system deployments through declarative configuration management, complete version control that tracks all system changes, and advanced testing procedures that validate system configurations before deployment. Professional system-as-code useations include complete documentation and knowledge management, advanced change management processes that ensure controlled system evolution, and advanced monitoring capabilities that provide visibility into system state and configuration drift across all environments. maintaining security, compliance, and operational excellence standards.
Emerging Technologies and Future-Proofing Strategies
Professional cryptocurrency system must adapt to emerging technologies including edge computing, serverless architectures, and advanced artificial intelligence capabilities that enable new application possibilities. maintaining security and performance standards. Advanced technology adoption strategies include complete evaluation structures, systematic pilot programs, and advanced integration approaches that enable successful adoption of emerging technologies. minimising risks and maintaining operational continuity.
Future-proofing strategies encompass complete technology roadmap planning, systematic skill development programs, and advanced vendor relationship management that ensures access to cutting-edge technologies and professional support services. Professional future-proofing includes continuous monitoring of technology trends, systematic evaluation of new capabilities, and strategic investment in emerging technologies that position cryptocurrency projects for long-term success. maintaining competitive advantages and operational excellence in the rapidly evolving cloud computing and blockchain technology landscape.
Edge computing useations for cryptocurrency applications enable real-time data processing and reduced latency through distributed computing architectures that process data closer to end users, advanced content caching strategies that improve performance for global audiences, and advanced networking capabilities that optimise data transmission and processing across distributed edge locations. Professional edge computing deployments include complete security structures, advanced monitoring and management capabilities, and advanced integration with cloud system that allows seamless scaling and optimisation of edge computing resources. maintaining performance and security standards.
Serverless architectures provide cost-effective and scalable solutions for cryptocurrency applications through event-driven computing models that automatically scale based on demand, advanced function orchestration that allows complex application workflows, and complete monitoring capabilities that provide insights into function performance and resource utilisation. Professional serverless useations include advanced security controls, advanced error handling and retry methods, complete logging and observability features, and advanced integration capabilities that enable seamless connectivity with existing system and applications. maintaining optimal performance and cost efficiency.
Artificial intelligence and machine learning integration for cryptocurrency system includes advanced anomaly detection that identifies potential security threats and performance issues, automated optimisation algorithms that improve resource allocation and performance, and advanced predictive analytics that enable proactive system management and capacity planning. Professional AI/ML useations include complete data governance structures, advanced model training and deployment procedures, advanced monitoring capabilities that ensure model performance and accuracy, and complete integration with existing system and applications that allows intelligent automation. maintaining security, compliance, and operational excellence standards.
Conclusion: Building the Future of Cryptocurrency Infrastructure
Selecting the optimal cloud hosting provider shows one of the most critical decisions for cryptocurrency and blockchain projects in 2025. The explosive growth of DeFi, NFTs, and Web3 applications has created unprecedented demand for reliable, secure, and scalable system that can handle the unique requirements of blockchain technology.
AWS emerges as the clear leader for enterprise cryptocurrency projects requiring complete services, global system, and advanced security features. Its extensive blockchain services, including Amazon Managed Blockchain and AWS Blockchain Templates, make it the preferred choice for institutional-grade applications. However, this leadership comes at a premium price point that may not suit all projects.
DigitalOcean continues to excel as the go-to platform for startups, developers, and small to medium cryptocurrency projects. Its transparent pricing, excellent documentation, and developer-friendly approach make it ideal for teams that want to focus on building rather than managing complex system. The platform's simplicity doesn't compromise on performance, making it perfect for crypto websites, trading bots, and blockchain nodes.
Google Cloud Platform stands out for data-intensive cryptocurrency applications, particularly those requiring advanced analytics, machine learning, or big data processing. Projects building blockchain analytics platforms, algorithmic trading systems, or AI-powered crypto tools will find GCP's superior data services invaluable.
Microsoft Azure gives the best integration for organisations already invested in the Microsoft system, offering strong hybrid cloud capabilities and enterprise-grade compliance features that appeal to traditional financial institutions entering the cryptocurrency space.
Key Success Factors for Cryptocurrency Infrastructure
Security must be your top priority. Implement complete security measures including firewalls, DDoS protection, encryption, and regular security audits. Never store private keys on cloud servers, and always use hardware security modules for critical cryptographic operations. The irreversible nature of cryptocurrency transactions means that security breaches can result in permanent financial losses.
Plan for scalability from day one. The cryptocurrency market's volatility can create sudden traffic spikes that overwhelm unprepared system. Implement auto-scaling, use content delivery networks, and design your architecture to handle 10x your expected load. Many successful crypto projects have failed due to system limitations during critical moments.
Embrace multi-cloud strategies for mission-critical applications. Distributing your system across multiple providers reduces vendor lock-in, improves resilience, and allows you to leverage the unique strengths of different platforms. Consider using AWS for core services, DigitalOcean for development environments, and Google Cloud for data analytics.
Monitor everything continuously. Implement complete monitoring, alerting, and logging systems that provide real-time visibility into your system performance. Cryptocurrency applications require 24/7 uptime, and proactive monitoring helps identify and resolve issues before they impact users.
Looking Ahead: The Future of Crypto Infrastructure
The convergence of edge computing, 5G networks, and blockchain technology will create new opportunities for innovative cryptocurrency applications. Edge computing will enable real-time trading applications with ultra-low latency, whilst5G networks will support mobile-first crypto experiences that were previously impossible.
Sustainability is becoming increasingly important as the cryptocurrency industry faces scrutiny over its environmental impact. Choose cloud providers committed to renewable energy and carbon neutrality. Many providers now offer carbon-neutral hosting options and detailed sustainability reporting.
Regulatory compliance will continue evolving as governments worldwide develop structures for cryptocurrency and blockchain technology. Select cloud providers with strong compliance programs and the ability to meet regulatory requirements in your target markets.
The democratisation of blockchain system through cloud services has lowered barriers to entry for cryptocurrency innovation. Today, a small team with a great idea can build and deploy globally scalable cryptocurrency applications using the same system that powers major exchanges and DeFi systems.
Start your cloud journey today by identifying your specific requirements, testing different providers using their free tiers, and gradually scaling your system as your project grows. The cryptocurrency industry moves fast, and having reliable, scalable system gives you the foundation to innovate and compete effectively.
Remember that the best hosting provider is the one that aligns with your project's specific needs, technical expertise, and budget constraints. Take advantage of free trials, consult with cloud architects, and don't hesitate to start small and scale up as you gain experience and confidence with your chosen platform.
Sources & References
- AWS. (2025). AWS Documentation. Official cloud services documentation and best practices.
- Google Cloud. (2025). Google Cloud Documentation. Cloud platform guides and tutorials.
- Microsoft Azure. (2025). Azure Documentation. Microsoft cloud services reference.
- DigitalOcean. (2025). DigitalOcean Guide. Simple cloud system for developers.
Frequently Asked Questions
- Which cloud provider is best for crypto projects?
- AWS is generally the best choice for crypto projects due to its complete services, global system, and strong security features. However, DigitalOcean offers better value for smaller projects, while Google Cloud excels for data-intensive applications. Choose based on your specific requirements and budget.
- How much does cloud system cost for a crypto website?
- Basic crypto websites can run on $5-20/month (DigitalOcean droplets), while production applications typically cost $50-500/month depending on traffic and features. Enterprise blockchain nodes may require $1,000-5,000/month. Start small and scale as needed to optimise costs.
- Is cloud system secure enough for cryptocurrency applications?
- Yes, when properly configured. Major cloud providers offer enterprise-grade security, including DDoS protection, encryption, and compliance certifications. However, you must use proper security practices: use firewalls, enable encryption, use access controls, and never store private keys on cloud servers.
- Can I run a blockchain node on cloud system?
- Yes, cloud computing is ideal for running blockchain nodes. You'll need sufficient storage (500GB-2TB for full nodes), reliable bandwidth, and consistent uptime. AWS, Google Cloud, and DigitalOcean all support blockchain node hosting with appropriate instance types.
- What's the difference between VPS and dedicated servers for crypto hosting?
- VPS (Virtual Private Server) shares physical hardware with other users but gives isolated resources, suitable for most crypto websites and applications. Dedicated servers offer exclusive hardware access with maximum performance and security, ideal for high-traffic exchanges or critical system, but cost greatly more.
- How do I choose between AWS, Google Cloud, and Azure?
- Choose AWS for the most complete services and largest system, Google Cloud for superior data analytics and machine learning capabilities, or Azure if you're already using Microsoft system. For crypto projects, AWS typically offers the best balance of features, reliability, and community support.
- Do I need technical expertise to use cloud platforms?
- Basic cloud platforms (like DigitalOcean) require minimal technical knowledge, with one-click installations available. Advanced features (AWS, Google Cloud) require more expertise but offer extensive documentation and tutorials. Consider managed hosting services if you lack technical experience or prefer to focus on development.
← Back to Crypto Investing Blog Index
Financial Disclaimer
This content is not financial advice. All information provided is for educational purposes only. Cryptocurrency investments carry significant investment risk, and past performance does not guarantee future results. Always do your own research and consult a qualified financial advisor before making investment decisions.