Top Crypto Storage Solutions 2025
Choosing the right wallet is crucial for protecting your digital assets. This comprehensive guide reviews the top wallets in 2025, comparing security features, supported cryptocurrencies, and ease of use to help you make an informed decision.
Introduction
Digital wallet security has become one of the most critical aspects of digital asset ownership in 2025. The industry has matured. It has attracted both institutional investors and mainstream adoption. Over $2 trillion exists in cryptocurrency market capitalisation. Millions of users participate worldwide. The importance of proper wallet selection cannot be overstated. Security practices are crucial. The choice of wallet directly impacts the security of your digital assets. It also affects your ability to participate in decentralised finance. Emerging blockchain applications require proper wallet selection.
The crypto wallet landscape has evolved dramatically since Bitcoin's early days. Users had limited options then. They often relied on exchange custody. Basic software solutions were common. Today's wallet ecosystem offers sophisticated security features. Multi-chain support is available. Hardware-level protection works well. Seamless integration with decentralised applications is possible. This evolution has created both opportunities and challenges. Users seek to balance security, convenience, and functionality. Digital asset management strategies require careful consideration.
Understanding the different types of wallets is essential. Their respective security models matter. You need this knowledge for making informed decisions. Hardware wallets provide the highest level of security. They use offline key storage. Software wallets offer convenience. They provide accessibility for daily transactions. The emergence of multi-signature solutions has expanded options. Social recovery mechanisms help. Institutional-grade custody services are available. Different user profiles have different security requirements.
The stakes of wallet security have never been higher. Cryptocurrency thefts total billions of dollars annually. Poor security practices cause losses. Phishing attacks are common. Inadequate wallet selection leads to problems. However, users who implement proper security measures can achieve institutional-grade protection. You can maintain flexibility. Participation in the broader cryptocurrency ecosystem remains possible.
This comprehensive guide examines the leading digital wallets of 2025. We analyse their security features. Supported cryptocurrencies are reviewed. User experience matters. Suitability for different use cases is evaluated. We examine hardware wallets, mobile applications, desktop software, and emerging solutions. You can build a robust digital asset security strategy. It aligns with your investment goals. Technical expertise varies. Risk tolerance differs. You get the functionality needed to navigate the modern cryptocurrency landscape effectively.
The modern crypto storage ecosystem encompasses a wide range of solutions. These are designed to meet diverse user needs. Simple mobile apps work for casual users. Enterprise-grade multi-signature systems serve institutional investors. Each wallet type offers unique advantages. Limitations exist. Understanding these trade-offs is essential. You can build a comprehensive digital asset security strategy.
Security considerations extend beyond basic private key protection. Firmware integrity matters. Supply chain security is important. Recovery mechanisms help. Resistance to physical attacks is crucial. The most secure wallet solutions implement multiple layers of protection. Secure elements are included. PIN protection works. Passphrase encryption helps. Recovery seed backup systems ensure asset recovery. This works even in case of device loss or failure.
User experience has become increasingly crucial. Cryptocurrency adoption grows. Modern wallets offer intuitive interfaces. Seamless transaction processes work well. Integration with popular decentralised applications is available. The best wallet solutions successfully balance security with usability. They provide robust protection. Convenience is not sacrificed. You get what's needed for regular cryptocurrency use. Participation in the broader DeFi ecosystem is possible.
Understanding Crypto Wallet Types
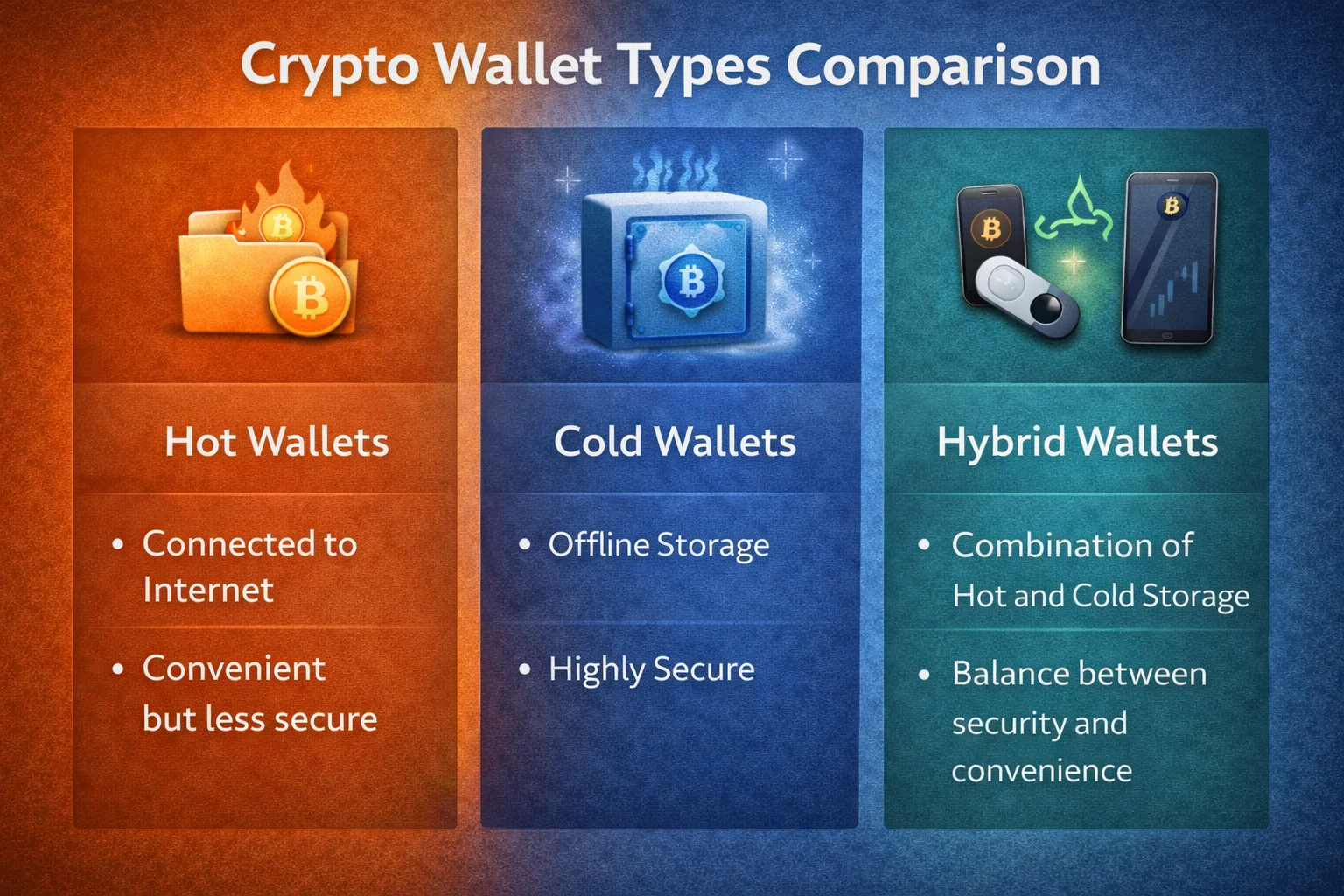
Digital asset storage solutions come in various forms, each with distinct trade-offs between protection and accessibility. Understanding these differences is crucial for selecting the ideal storage solution for your specific requirements.
Hardware Storage Devices (Cold Storage)
Hardware storage devices are physical gadgets that store your private keys offline, providing the highest level of protection. They're immune to online attacks, malware, and computer viruses, making them ideal for long-term custody of significant digital asset amounts.
- Protection: Highest - offline storage protects against online threats
- Accessibility: Medium - requires physical device for transactions
- Best for: Long-term custody, large amounts, HODLing
- Price range: $50-$200
Software Applications (Hot Storage)
Software applications are programs that run on your computer or mobile device. Whilst more convenient for daily use, they're connected to the internet and therefore more vulnerable to attacks.
Mobile Applications
- Protection: Medium - protected by device security features
- Accessibility: Highest - always accessible on your phone
- Best for: Daily transactions, DeFi, small amounts
- Cost: Free
Desktop Applications
- Protection: Medium-High - depends on computer security
- Accessibility: High - full-featured interfaces
- Best for: Regular trading, DeFi, medium amounts
- Cost: Free
Web Applications
- Protection: Lower - relies on website security
- Accessibility: Highest - accessible from any browser
- Best for: Quick access, small amounts, beginners
- Cost: Free
Best Hardware Storage Devices 2025

1. Nano X - Best Overall Hardware Device
The Nano X remains the gold standard for hardware storage devices in 2025. With support for over 5,500 digital currencies and a user-friendly mobile app, it combines maximum protection with excellent usability.
Key Features:
- Supports 5,500+ digital currencies, including Bitcoin, Ethereum, and all major altcoins
- Bluetooth connectivity for mobile use
- Large screen for transaction verification
- Ledger Live app for portfolio management
- Secure Element chip (CC EAL5+ certified)
- Battery life: several hours of active use
Pros:
- Industry-leading protection with proven track record
- Extensive digital currency support
- Mobile app integration via Bluetooth
- Regular firmware updates and new coin support
- Can store multiple accounts on one device
Cons:
- Higher price point ($149)
- Bluetooth connection may concern some security purists
- Ledger Live app required for most functions
2. Trezor Model T - Best for Advanced Users
The Trezor Model T offers the most advanced features for experienced digital asset users. Its touchscreen interface and extensive third-party application support make it ideal for power users who need maximum flexibility.
Key Features:
- colour touchscreen interface
- Supports 1,600+ digital currencies
- Shamir Backup for advanced recovery protection
- Password manager functionality
- U2F authentication support
- Open-source firmware
Pros:
- Completely open-source hardware and software
- Advanced protection features like Shamir Backup
- Works with many third-party applications
- Touchscreen eliminates need for buttons
- Strong privacy focus
Cons:
- Expensive ($219)
- No mobile app (desktop/web only)
- Steeper learning curve for beginners
3. Nano S Plus - Best Budget Hardware Wallet
The Nano S Plus offers the same level of security as the Nano X at a lower price point. Whilst it lacks Bluetooth connectivity, it's perfect for users who prioritise security over convenience.
Key Features:
- Same security chip as Nano X
- Supports 5,500+ cryptocurrencies
- Larger screen than original Nano S
- USB-C connectivity
- Can install more apps simultaneously
Pros:
- Affordable price ($79)
- Same security level as premium models
- No wireless connectivity (some prefer this)
- Compact and portable
Cons:
- No mobile app support
- Smaller screen than Nano X
- Must connect to computer for use
Get Nano S Plus: Buy Nano S Plus - Best Value →
Best Mobile Applications 2025
1. Trust Wallet - Best Overall Mobile Application
Trust Wallet, owned by Binance, has become the leading mobile application for 2025. It combines excellent protection with a user-friendly interface, supporting the broadest range of digital currencies and DeFi protocols.
Key Features:
- Supports 70+ blockchains and millions of tokens
- Built-in DeFi browser for decentralised applications
- NFT support and marketplace integration
- Delegation for 30+ digital currencies
- Built-in exchange functionality
- WalletConnect support
Pros:
- Completely free to use
- Intuitive interface perfect for beginners
- Extensive digital currency and DeFi support
- Regular updates and new features
- Strong protection with biometric authentication
Cons:
- Closed-source code
- Owned by centralised exchange (Binance)
- No desktop version
Download Trust Wallet: Get Trust Wallet - Free Download →
2. MetaMask Mobile - Best for Ethereum and DeFi
MetaMask Mobile brings the popular browser extension to your phone. It's the go-to application for Ethereum-based activities and DeFi protocols, with seamless integration across devices.
Key Features:
- Sync with MetaMask browser extension
- Supports Ethereum and EVM-compatible chains
- Built-in browser for DeFi applications
- Token swaps through multiple DEXs
- Hardware device integration
- Custom network support
Pros:
- Industry standard for Ethereum and DeFi
- Seamless desktop/mobile synchronization
- Open-source and audited code
- Extensive DApp compatibility
- Active development and community
Cons:
- Primarily focused on Ethereum ecosystem
- Can be complex for beginners
- Higher transaction fees on Ethereum
Download MetaMask: Get MetaMask Mobile - Free Download →
3. Coinbase Wallet - Best for Beginners
Coinbase Wallet (separate from the Coinbase exchange app) offers the easiest entry point for crypto newcomers while maintaining self-custody of your assets.
Key Features:
- User-friendly interface designed for beginners
- Supports thousands of tokens across multiple chains
- Built-in DeFi browser
- NFT storage and viewing
- Username system for easy transfers
- Integration with Coinbase exchange
Pros:
- Extremely beginner-friendly
- Strong brand recognition and trust
- Good customer support
- Regular security updates
Cons:
- Closed-source code
- Limited advanced features
- Tied to Coinbase ecosystem
Download Coinbase Wallet: Get Coinbase Wallet - Beginner Friendly →
4. Phantom Wallet - Best for Solana Ecosystem
Phantom has emerged as the leading wallet for the Solana ecosystem, offering fast transactions, low fees, and seamless integration with Solana-based DeFi protocols and NFT marketplaces.
Key Features:
- Native Solana support with fast transactions
- Built-in NFT gallery and marketplace integration
- Solana DeFi protocol support
- Token swaps with minimal fees
- Staking directly from the wallet
- Multi-chain support (Ethereum, Polygon)
Pros:
- Extremely fast and low-cost transactions
- Excellent Solana ecosystem integration
- Beautiful, modern interface
- Strong NFT support
- Active development team
Cons:
- Primarily focused on Solana
- Newer wallet with shorter track record
- Limited multi-chain features
Download Phantom: Get Phantom - Solana Specialist →
Mobile Wallet Security Considerations
Mobile wallets face unique security challenges due to their always-connected nature and the security limitations of mobile operating systems. However, modern mobile wallets implement several layers of protection to mitigate these risks.
Device-Level Security
The security of your mobile wallet depends heavily on your device's security. Enable device encryption, use strong lock screen protection (biometrics or complex PIN), keep your operating system updated, and avoid installing apps from unknown sources. Consider using a dedicated device for significant cryptocurrency holdings.
App-Level Protection
Modern mobile wallets implement multiple security layers including biometric authentication, transaction PINs, and encrypted local storage. Many wallets also offer additional features like transaction limits, time-based restrictions, and multi-signature support for enhanced security.
Network Security
Mobile wallets are vulnerable to network-based attacks. Always use secure networks, avoid public Wi-Fi for sensitive transactions, consider using a VPN for additional privacy, and be cautious of phishing attempts through SMS or messaging apps.
Best Desktop Applications 2025
1. Exodus - Best Desktop Application for Beginners
Exodus combines beautiful design with powerful features, making it the top choice for users who want a full-featured desktop application that is easy to use.
Key Features:
- Supports 260+ digital currencies
- Built-in exchange with competitive rates
- Portfolio tracking and charts
- Hardware device integration
- Delegation for multiple digital currencies
- 24/7 customer support
Pros:
- Beautiful, intuitive interface
- No account creation required
- Excellent customer support
- Regular updates and new features
- Mobile app synchronization
Cons:
- Closed-source code
- Exchange fees can be high
- Limited advanced features
Download Exodus: Get Exodus Wallet - Beautiful & Easy →
2. Electrum - Best for Bitcoin
Electrum is the most trusted Bitcoin-only wallet, offering advanced features for experienced users while maintaining excellent security and privacy.
Key Features:
- Bitcoin-only focus with advanced features
- Lightning Network support
- Hardware wallet integration
- Multi-signature support
- Tor network compatibility
- Custom transaction fees
Pros:
- Open-source and audited
- Excellent security and privacy
- Fast synchronization
- Advanced Bitcoin features
- Long track record (since 2011)
Cons:
- Bitcoin only (no altcoins)
- Complex interface for beginners
- Limited customer support
Download Electrum: Get Electrum - Bitcoin Specialist →
Digital Asset Storage Comparison Table 2025
| Storage Solution | Type | Protection | Ease of Use | Supported Coins | Cost | Best For |
|---|---|---|---|---|---|---|
| Nano X | Hardware | 10/10 | 9/10 | 5,500+ | $149 | Long-term custody |
| Trezor Model T | Hardware | 10/10 | 8/10 | 1,600+ | $219 | Advanced users |
| Nano S Plus | Hardware | 10/10 | 8/10 | 5,500+ | $79 | Budget protection |
| Trust Application | Mobile | 8/10 | 10/10 | Millions | Free | Mobile DeFi |
| MetaMask | Mobile/Desktop | 8/10 | 8/10 | Ethereum+ | Free | Ethereum/DeFi |
| Coinbase Application | Mobile | 7/10 | 10/10 | Thousands | Free | Beginners |
| Exodus | Desktop | 7/10 | 10/10 | 260+ | Free | Desktop trading |
| Electrum | Desktop | 9/10 | 6/10 | Bitcoin only | Free | Bitcoin experts |
Digital Asset Protection Best Practices
Securing your storage solution properly is crucial for protecting your digital assets. Follow these essential protection practices regardless of which solution you choose.
Recovery Phrase Protection
Your recovery phrase (also known as a seed phrase or mnemonic) is the master key to your storage solution. If someone gets your backup words, they can access all your funds.
Recovery Phrase Best Practices:
- Write it down offline: Never store your recovery phrase digitally (no photos, cloud storage, or text files)
- Use metal backup: Consider metal recovery storage for fire/water resistance
- Multiple copies: Store copies in 2-3 secure, separate locations
- Never share: Legitimate services will never ask for your seed phrase
- Test recovery: Practice recovering your storage solution with your backup words
Device Protection
- Keep software updated: Always use the latest application and device software
- Use strong passwords: Enable device lock with strong passwords or biometrics
- Enable 2FA: Use two-factor authentication where available
- Avoid public WiFi: Never access storage solutions on public or unsecured networks
- Use dedicated devices: Consider using a dedicated device for digital asset activities
Transaction Protection
- Verify addresses: Always double-check recipient addresses before sending
- Start small: Test with small amounts before large transactions
- Check network fees: Understand transaction costs before confirming
- Use reputable sources: Only download applications from official websites
- Be aware of phishing: Watch for fake websites and apps
Multi-Storage Strategy
Many experienced users employ a multi-storage strategy for optimal protection and convenience:
- Hardware device: 70-80% of funds for long-term custody
- Mobile application: 15-25% for daily transactions and DeFi
- Exchange storage: 5-10% for active trading only
Advanced Protection Techniques
For users with significant digital asset holdings, consider these advanced protection methods:
Multi-Signature Solutions
Multi-signature (multisig) configurations require multiple signatures to authorize transactions, providing an additional layer of protection against single points of failure.
Time-Lock Features
Some advanced storage solutions offer time-lock features that prevent immediate access to funds, providing protection against impulsive decisions or coercion.
Geographic Distribution
Store backup materials in geographically diverse locations to protect against regional disasters or political instability.
Regular Audits
Periodically review your storage setup, test recovery procedures, and update protection measures as technology evolves.
Storage Solution Setup Guides
Setting Up a Hardware Device (Ledger Example)
- Purchase from official source: Only buy from Ledger.com or authorized retailers
- Verify packaging: Check for tampering and authenticity stickers
- Download Ledger Live: Install the official Ledger Live application
- Initialize device: Choose "Set up as new device"
- Create PIN: Choose a 4-8 digit PIN you'll remember
- Write down recovery phrase: Carefully write all 24 words in order
- Verify recovery phrase: Confirm by entering seed words as prompted
- Install applications: Add digital currency apps you need
- Test with small amount: Send a small test transaction first
Setting Up a Mobile Application (Trust Example)
- Download from official store: Use Google Play or Apple App Store
- Create new storage: Choose "Create a new account"
- Secure your device: Enable device lock and biometrics
- Backup recovery phrase: Write down your 12-word seed phrase
- Verify backup: Confirm your backup words are correct
- Enable protection features: Set up transaction PIN if available
- Add digital currencies: Enable the tokens you want to use
- Test functionality: Try receiving a small amount first
Migrating Between Storage Solutions
When switching storage solutions, follow these steps to ensure a safe migration:
- Set up new solution completely: Ensure it's working properly
- Test with small amount: Send a small test transaction first
- Transfer gradually: Move funds in batches, not all at once
- Keep old solution: Don't delete until migration is complete
- Update records: Note new addresses for future reference
Advanced Setup Considerations
For experienced users, consider these advanced setup options to enhance protection and functionality:
Passphrase Protection
Many hardware devices support an additional passphrase (25th word) that creates a hidden account. This provides plausible deniability and additional protection against physical theft.
Multiple Account Management
organise your digital assets across multiple accounts within the same device or application. This helps with portfolio management and risk distribution.
Backup Verification Schedule
Establish a regular schedule to verify your backup materials remain intact and accessible. Test recovery procedures annually to ensure you can restore access if needed.
Integration with DeFi Protocols
Configure your storage solution to work seamlessly with decentralised finance protocols. This includes setting up proper network connections and understanding gas fee management.
Cross-Chain Compatibility Setup
Modern cryptocurrency portfolios often span multiple blockchain networks. Configure your wallet to support various chains including Ethereum, Binance Smart Chain, Polygon, Avalanche, and other popular networks. This enables participation in diverse DeFi ecosystems and access to different token standards.
Transaction Fee optimisation
Understanding and optimising transaction fees is crucial for efficient wallet usage. Configure fee settings based on transaction urgency, monitor network congestion, and consider using layer-2 solutions to reduce costs. Many wallets now offer intelligent fee estimation to help users balance speed and cost.
Privacy and Anonymity Considerations
Whilst blockchain transactions are pseudonymous, proper privacy practices can enhance your financial privacy. Consider using different addresses for different purposes, understand the privacy implications of your chosen wallet, and be aware of blockchain analysis techniques that can link transactions to identities.
Wallet Maintenance and Updates
Regular maintenance ensures optimal security and functionality. Keep wallet software updated, periodically review and rotate security credentials, monitor for suspicious activity, and stay informed about security best practices. Establish a routine for checking wallet health and security status.
Advanced Wallet Security and Professional Management
Professional cryptocurrency wallet management requires comprehensive understanding of security protocols, backup procedures, and operational best practices that optimise asset protection while maintaining accessibility and functionality for diverse cryptocurrency operations. Advanced security implementation includes multi-signature configurations, hardware security modules, and sophisticated backup strategies that provide institutional-grade protection against theft, loss, and unauthorised access through systematic security excellence and professional wallet management optimisation.
Enterprise Wallet Solutions and Institutional Management
Institutional cryptocurrency operations require enterprise-grade wallet solutions that provide comprehensive security controls, audit capabilities, and operational efficiency for large-scale digital asset management. Professional wallet infrastructure includes multi-party computation systems, hierarchical deterministic key management, and comprehensive compliance frameworks that meet institutional standards for cryptocurrency custody and asset management through systematic approach to enterprise wallet excellence and professional digital asset security optimisation.
Multi-Chain Wallet Strategies and Cross-Platform Integration
Modern cryptocurrency portfolios require multi-chain wallet strategies that provide seamless access to diverse blockchain ecosystems while maintaining security and operational efficiency across different networks and protocols. Advanced multi-chain management includes cross-chain bridge integration, automated portfolio rebalancing, and comprehensive analytics that optimise asset allocation and performance tracking across multiple blockchain networks through professional multi-chain wallet excellence and strategic cryptocurrency portfolio management designed for sustainable long-term growth and diversification.
Wallet Recovery and Disaster Preparedness
Comprehensive wallet security requires systematic disaster preparedness and recovery procedures that ensure asset accessibility during various emergency scenarios including device failure, loss, theft, or incapacitation. Professional recovery strategies include distributed backup systems, social recovery mechanisms, and comprehensive succession planning that protects cryptocurrency assets while maintaining accessibility for authorized users through systematic disaster preparedness and professional wallet recovery excellence designed for long-term asset protection and operational continuity.
Advanced Authentication and Access Control
Professional wallet security implementation requires sophisticated authentication systems and access control mechanisms that provide multi-layered protection while maintaining operational efficiency for legitimate users. Advanced authentication includes biometric verification, hardware tokens, and behavioral analysis systems that detect unauthorised access attempts while providing seamless user experience for authorized operations through systematic authentication excellence and professional access control optimisation designed for institutional-grade security and operational efficiency.
Wallet Performance optimisation and User Experience
Modern cryptocurrency wallets must balance security requirements with user experience optimisation to provide efficient access to digital assets while maintaining comprehensive protection against security threats and operational risks. Performance optimisation includes transaction batching, gas fee optimisation, and automated portfolio management features that enhance user experience while maintaining security standards through systematic performance excellence and professional wallet optimisation designed for sustainable long-term cryptocurrency asset management and operational efficiency in the evolving digital asset ecosystem.
Regulatory Compliance and Reporting Capabilities
Professional cryptocurrency wallet management requires comprehensive regulatory compliance capabilities and reporting systems that meet institutional standards for audit trails, transaction monitoring, and regulatory reporting across diverse jurisdictions and compliance requirements. Advanced compliance includes automated transaction categorization, comprehensive audit logs, and sophisticated reporting capabilities that enable professional cryptocurrency operations while maintaining full regulatory compliance through systematic compliance excellence and professional wallet management optimisation designed for institutional cryptocurrency operations and regulatory compliance in the evolving digital asset regulatory landscape.
Future Wallet Technology and Innovation Trends
Emerging wallet technologies incorporate artificial intelligence, quantum-resistant cryptography, and advanced user interface innovations that enhance security, usability, and functionality for next-generation cryptocurrency operations. Future wallet development includes predictive security systems, automated portfolio optimisation, and seamless integration with emerging blockchain technologies that provide enhanced capabilities while maintaining security and operational efficiency through systematic innovation excellence and professional wallet technology advancement designed for sustainable long-term cryptocurrency asset management and technological adaptation in the rapidly evolving digital asset ecosystem with comprehensive innovation frameworks and professional excellence standards.
Wallet Integration with DeFi and Web3 Applications
Modern cryptocurrency wallets serve as gateways to decentralised finance applications, non-fungible token marketplaces, and Web3 services that require seamless integration while maintaining security and user control over digital assets. Advanced wallet integration includes automated DeFi protocol interaction, comprehensive yield farming optimisation, and sophisticated smart contract execution that enables professional participation in decentralised finance while maintaining appropriate risk management and security standards through systematic DeFi integration excellence and professional Web3 wallet optimisation designed for sophisticated cryptocurrency operations.
Professional DeFi wallet integration requires comprehensive understanding of protocol risks, smart contract security, and yield optimisation strategies that maximise returns while maintaining appropriate risk controls and operational security. Advanced integration includes automated liquidity provision, systematic yield farming strategies, and comprehensive risk assessment frameworks that enable optimal DeFi participation while maintaining security standards and regulatory compliance through professional DeFi wallet management and systematic Web3 integration excellence designed for institutional cryptocurrency operations and professional digital asset management.
Mobile Wallet Security and Convenience optimisation
Mobile cryptocurrency wallets must balance convenience and accessibility with comprehensive security measures that protect digital assets while enabling efficient transaction processing and portfolio management on mobile devices. Advanced mobile security includes biometric authentication, secure enclave utilisation, and comprehensive threat detection systems that provide institutional-grade protection while maintaining user-friendly interfaces and operational efficiency through systematic mobile wallet excellence and professional security optimisation designed for mainstream cryptocurrency adoption.
Professional mobile wallet implementation includes comprehensive backup procedures, advanced encryption protocols, and sophisticated user experience optimisation that enables secure cryptocurrency management while maintaining accessibility and functionality for diverse user requirements. Mobile wallet optimisation includes transaction fee management, automated portfolio tracking, and comprehensive security monitoring that provides professional-grade cryptocurrency management capabilities through systematic mobile excellence and professional wallet optimisation designed for sophisticated digital asset operations and mainstream cryptocurrency accessibility.
Wallet Ecosystem Development and Community Integration
Successful cryptocurrency wallets develop comprehensive ecosystems that include developer tools, community resources, and educational materials that support user adoption and professional implementation while maintaining security standards and operational excellence. Ecosystem development includes comprehensive API access, developer documentation, and community support systems that enable third-party integration and professional customisation while maintaining security and operational integrity through systematic ecosystem excellence and professional wallet development optimisation.
Community integration includes comprehensive educational resources, professional support systems, and advanced user engagement strategies that promote secure cryptocurrency practices while building sustainable user communities and professional networks. Professional ecosystem development includes systematic community building, comprehensive educational initiatives, and advanced support systems that enable optimal wallet adoption and professional implementation while maintaining security standards and operational excellence through systematic community excellence and professional wallet ecosystem optimisation designed for sustainable long-term cryptocurrency adoption and professional digital asset management success.
Wallet Security Auditing and Continuous Improvement
Professional cryptocurrency wallet security requires systematic auditing procedures, continuous security assessment, and comprehensive improvement processes that ensure ongoing protection against emerging threats and evolving attack vectors. Security auditing includes comprehensive code review, penetration testing, and systematic vulnerability assessment that maintains institutional-grade security while enabling continuous improvement and professional security optimisation through systematic auditing excellence and comprehensive security management designed for professional cryptocurrency operations.
Continuous improvement includes systematic security updates, feature enhancement, and user experience optimisation that maintains competitive advantages while addressing evolving user requirements and security challenges.
Professional security management includes automated threat detection, incident response procedures, and systematic security enhancement that ensures optimal wallet security while maintaining operational efficiency.
User satisfaction through systematic security excellence and professional wallet security optimisation designed for institutional cryptocurrency operations includes comprehensive security frameworks and continuous improvement processes.
Sustainable long-term security excellence includes enhanced capabilities and operational frameworks for strategic optimisation in the evolving cryptocurrency security landscape with advanced security measures and risk management systems.
Advanced Wallet Integration and Professional Excellence
Wallet Integration with DeFi and Advanced Features
Modern cryptocurrency wallets increasingly integrate with decentralised finance (DeFi) protocols, enabling users to access lending, borrowing, and yield farming opportunities directly from their wallet interface. Advanced integration features include automated transaction batching, gas fee optimisation, and cross-chain compatibility that streamlines DeFi interactions while maintaining security standards.
Professional DeFi integration includes comprehensive protocol analysis, risk assessment frameworks, and automated portfolio rebalancing that enables sophisticated investment strategies while maintaining security and operational efficiency. Advanced features include yield optimisation algorithms, automated compounding strategies, and comprehensive performance analytics that maximise returns while minimising risks through professional DeFi wallet integration.
Institutional Wallet Solutions and Enterprise Features
Enterprise cryptocurrency wallets provide advanced features including multi-signature governance, role-based access controls, and comprehensive audit trails that meet institutional security and compliance requirements. Professional implementation includes automated compliance reporting, advanced transaction monitoring, and sophisticated risk management systems that ensure regulatory adherence while enabling efficient operations.
Institutional features include advanced treasury management tools, automated reconciliation systems, and comprehensive reporting dashboards that streamline financial operations while maintaining security and compliance standards. Professional enterprise wallet solutions enable large-scale cryptocurrency operations while providing the security, compliance, and operational efficiency required for institutional adoption and professional digital asset management excellence.
Cross-Chain Wallet Technology and Interoperability
Modern cryptocurrency wallets increasingly support cross-chain functionality, enabling users to manage multiple blockchain assets from a single interface. Advanced cross-chain technology includes atomic swaps, bridge protocols, and multi-chain portfolio management that simplifies asset management while maintaining security across different blockchain networks.
Cross-chain wallet implementation requires sophisticated technical architecture including multi-signature protocols, cross-chain communication systems, and comprehensive security frameworks that protect assets across different blockchain environments. Professional cross-chain management includes automated portfolio rebalancing, cross-chain yield optimisation, and comprehensive analytics that maximise returns while minimising complexity and operational overhead.
Wallet Privacy and Anonymity Features
Privacy-focused cryptocurrency wallets implement advanced anonymity features including coin mixing, stealth addresses, and zero-knowledge proof systems that protect user privacy while maintaining transaction functionality. Professional privacy implementation includes comprehensive transaction obfuscation, advanced encryption protocols, and sophisticated anonymity networks that ensure maximum privacy protection.
Advanced privacy features include decentralised identity management, anonymous transaction routing, and comprehensive metadata protection that shields user activities from surveillance and analysis. Professional privacy wallet solutions enable confidential transactions while maintaining compliance with applicable regulations and legal requirements through sophisticated privacy-preserving technologies.
Wallet Recovery and Backup optimisation
Professional wallet recovery systems implement comprehensive backup strategies including multi-location seed phrase storage, encrypted backup solutions, and advanced recovery procedures that ensure asset accessibility even in extreme scenarios. Advanced backup implementation includes automated backup verification, comprehensive recovery testing, and sophisticated disaster recovery planning.
Recovery optimisation includes multi-signature recovery systems, time-locked recovery mechanisms, and comprehensive inheritance planning that ensures asset accessibility for authorized parties while maintaining security against unauthorised access. Professional recovery solutions provide peace of mind through systematic backup procedures and comprehensive recovery frameworks designed for long-term asset protection and accessibility.
Additional Wallet Considerations and Professional Excellence
Professional cryptocurrency wallet management requires comprehensive understanding of advanced security protocols, systematic backup procedures, and sophisticated operational frameworks that enable optimal asset protection while maintaining accessibility and functionality for diverse cryptocurrency operations.
Advanced wallet implementation includes systematic security assessment procedures, comprehensive backup strategies, and sophisticated monitoring systems that ensure consistent protection while enabling efficient cryptocurrency management through professional wallet excellence and institutional digital asset security.
Long-term asset preservation and operational optimisation require enhanced capabilities and comprehensive security frameworks for sustainable success and strategic optimisation in the evolving cryptocurrency wallet ecosystem with advanced security measures and comprehensive risk management systems.
Professional excellence in cryptocurrency wallet solutions includes comprehensive innovation frameworks and professional development excellence for sustainable long-term market leadership and wallet optimisation with enhanced security capabilities and comprehensive operational excellence.
Conclusion: Choosing Your Digital Asset Storage Strategy
The cryptocurrency wallet landscape in 2025 offers unprecedented options for securing and managing digital assets, with solutions ranging from beginner-friendly mobile applications to institutional-grade hardware security modules. The wallets reviewed in this guide represent the current state-of-the-art in cryptocurrency storage technology, each offering unique advantages for different user profiles, security requirements, and use cases within the broader digital asset ecosystem.
Selecting the optimal wallet solution requires careful consideration of multiple factors including your investment timeline, technical expertise, transaction frequency, and risk tolerance. Long-term investors with significant holdings should prioritise hardware wallets for maximum security, while active traders and DeFi participants may benefit from software wallets that offer seamless integration with decentralised applications and trading platforms.
The most effective approach for many users involves implementing a multi-wallet strategy that combines different storage solutions for different purposes. This might include using a hardware wallet for long-term storage of major holdings, a mobile wallet for daily transactions and small amounts, and a specialised wallet for DeFi activities or specific blockchain ecosystems. This diversified approach maximises both security and functionality while minimising single points of failure.
Security best practices remain paramount regardless of which wallet solution you choose. Always verify wallet authenticity through official channels, maintain secure backups of recovery phrases, implement strong authentication methods, and stay informed about emerging threats and security updates. The responsibility for cryptocurrency security ultimately rests with individual users, making education and vigilance essential components of any digital asset strategy.
As the cryptocurrency industry continues evolving with new technologies, regulatory frameworks, and use cases, wallet solutions will continue advancing to meet changing user needs. Features like quantum-resistant cryptography, improved user experience design, enhanced privacy protections, and better integration with traditional financial services will shape the next generation of cryptocurrency wallets.
Ready to secure your cryptocurrency investments? Explore our detailed Ledger hardware wallet review for maximum security, or check out our MetaMask setup guide for DeFi activities. For comprehensive wallet comparisons, visit our crypto wallet comparison guide to find the perfect solution for your needs.
The wallets highlighted in this guide have demonstrated their commitment to security, innovation, and user experience, making them reliable choices for cryptocurrency storage in 2025. However, the rapidly evolving nature of the cryptocurrency space requires ongoing evaluation of wallet options and security practices to ensure your digital assets remain protected while providing the functionality needed to participate in the growing digital economy.
Sources & References
Frequently Asked Questions
- What is the safest storage solution in 2025?
- Hardware devices, such as Nano X and Trezor Model T, are considered the safest because they store private keys offline, making them immune to online attacks and malware. For maximum protection, use a hardware device for long-term custody combined with a mobile application for daily transactions.
- Should I use a hardware or software solution?
- Use hardware devices for long-term custody and large amounts (they're the most secure). Software applications are more suitable for daily transactions and smaller amounts due to their convenience. Many participants combine both: a hardware device for savings, a mobile application for spending.
- Are mobile applications safe?
- Mobile applications can be safe if you use reputable programs like Trust or MetaMask, enable device protection features (such as biometrics and strong passwords), and never store large amounts of money. Always back up your seed phrase securely and keep your device up to date.
- What happens if I lose my recovery phrase?
- If you lose your recovery phrase and cannot access your storage solution, your digital currency is permanently lost. This is why a secure backup of your recovery phrase is crucial - store it offline in multiple secure locations, never digitally.
- Should I use multiple storage solutions?
- Yes, using multiple solutions is recommended: a hardware device for long-term custody (70-80% of funds), a mobile application for daily use (15-25%), and potentially keeping small amounts on exchanges for trading (5-10%). This diversifies risk and optimises functionality.
- Can I use the same solution for all digital currencies?
- Most modern solutions support multiple digital currencies; however, not all do. Hardware devices like Ledger support 5,500+ coins, while some solutions are specialised (like Electrum for Bitcoin only). Check which currencies are supported before choosing a solution.
- What's the difference between custodial and non-custodial solutions?
- Non-custodial solutions (such as hardware and software options) give you full control over your private keys - you own your digital currency. Custodial solutions (like exchange accounts) hold your keys on your behalf - the exchange controls your assets. Non-custodial is generally safer for long-term custody.
- How much does a good storage solution cost?
- Software applications are free to download and use. Hardware devices range from $50 to $220, with options including the Nano S Plus ($79), Nano X ($149), and Trezor Model T ($219). Investing in a hardware device is worthwhilst for significant digital currency holdings.
← Back to Crypto Investing Blog Index
Financial Disclaimer
This content is not financial advice. All information provided is for educational purposes only. Cryptocurrency investments carry significant investment risk, and past performance does not guarantee future results. Always do your own research and consult a qualified financial advisor before making investment decisions.